Cloudflare has been brought up today with a new news of cyber-attack, following the recent cyber attack. Come to the details of the new cyber attack, about twice the size of the previous attack, which was described as 'the biggest', together.
Cloudflare serves many companies against attacks that are being organized and organized online. The size of these attacks on companies can be quite surprising. One of the biggest social media problems of our time, the biggest of these cyber attacks, is also announced by Cloudflare.
A recent announcement by Cloudflare reported that they were facing the biggest cyber attack ever. Following a successful cyberattack, a much larger attack has been reportedly prevented today.

26 million requests per second reported
In the previous attack, 15 million requests were reported to the site and this was announced as one of the largest DDoS attacks ever. However, a recent statement has reported that there has been another attack that would leave even this attack in its shadow. Cloudflare announced that 26 million requests per second were received in this attack. These requests sent by malicious individuals were soon identified.
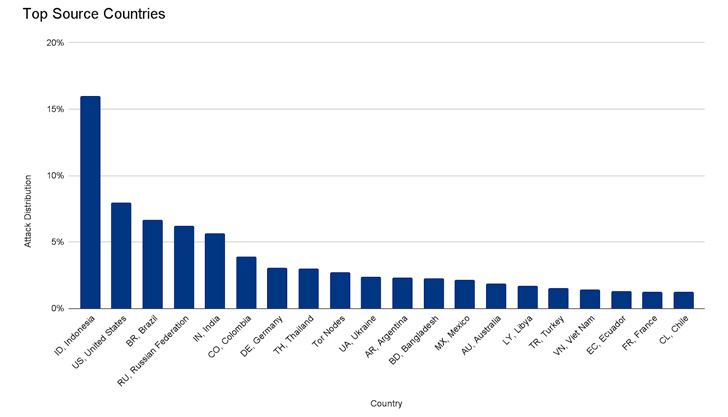
The sources of the attacks were determined to come from a total of 121 countries, particularly Indonesia, the United States, Brazil and Russia. Cloudflare means that attacks are organized through HTTPS, which costs more money to start and prevent attacks. 3% of the attacks were carried out through Tor connections.
Cloudflare reported that as few customers were affected by the attack as possible and that the attack was soon discovered and necessary measures were taken.

Cloudflare Saw Record-Breaking DDoS Attack Peaking at 26 Million Request Per Second
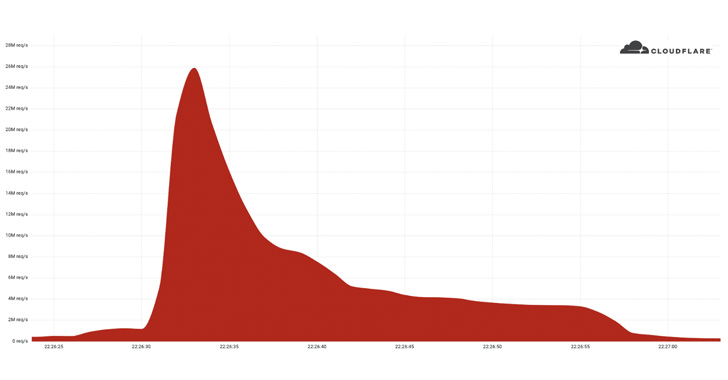
Last week, 26 million requests per second (RPS) took action to prevent a distributed denial of service (DDoS) attack, and it was the largest HTTPS DDoS attack ever detected, Cloudflare said on Tuesday.
Web performance and security company said the attack was aimed at an anonymous customer website using the Free plan, and was caused by a "powerful" botnet, which consists of 5,067 devices each node produces around 5,200 RPS at the summit.
The botnet is said to have flooded more than 212 million HTTPS requests in less than 30 seconds from more than 1,500 networks in 121 countries, including Indonesia, the United States, Brazil, Russia and India. Roughly 3% of the attack came from Tor nodes.
Omar Yoachimik of Cloudflare said the attack was "mostly caused by Cloud Service Providers, unlike residential Internet Service Providers, using kidnapped virtual machines and powerful servers to create the attack - unlike much weaker Internet of things (IoT) devices."
Initiating HTTPS-based DDoS attacks tends to be more expensive in terms of computing due to the higher cost associated with establishing a secure TLS encrypted connection.
This is the second volumetric HTTPS DDoS attack blocked by Cloudflare in months. In late April 2022, he said he had defused 15.3 million RPS HTTPS DDoS attacks against a customer who ran the crypto launch ramp.
According to the company's Q1 2022 DDoS attack trends report, volumetric DDoS attacks over 100 gigabit per second (gbps) increased by up to 645% per quarter.
"Attacks with high bit rates try to overwhelm servers, routers, or other in-line hardware devices with high packet rates, while trying to disrupt the Internet connection and cause a denial of service event," researchers said.
"In this case, the packages are 'dropped', which means the device cannot process them. For users, this causes service interruptions and denial of service."
Turkish Version: Click
Son düzenleme: