- 7 Tem 2013
- 8,208
- 4
- 690
Cyber Kill Chain
Today I'm going to talk about Cyber Kill Chain. It is very important topic for you, if you want to become a hacker.

What is Cyber Kill Chain?
The cyber kill chain is a series of steps that trace stages of a cyberattack from the early reconnaissance stages to the exfiltration of data. The kill chain helps us to understand combat ransomware, security breaches, and advanced persistent attacks (APTs). The Cyber Kill Chain consist of 7 sections.

Cyber Kill Chain Stages
Discovery
Arming
Transmission
Exploitation
Setup
Command and Control
Targeted Action

Discovery
The attackers begin to investigate the victim's information. They start with searching the system and this is the first stage of the cyber kill chain.
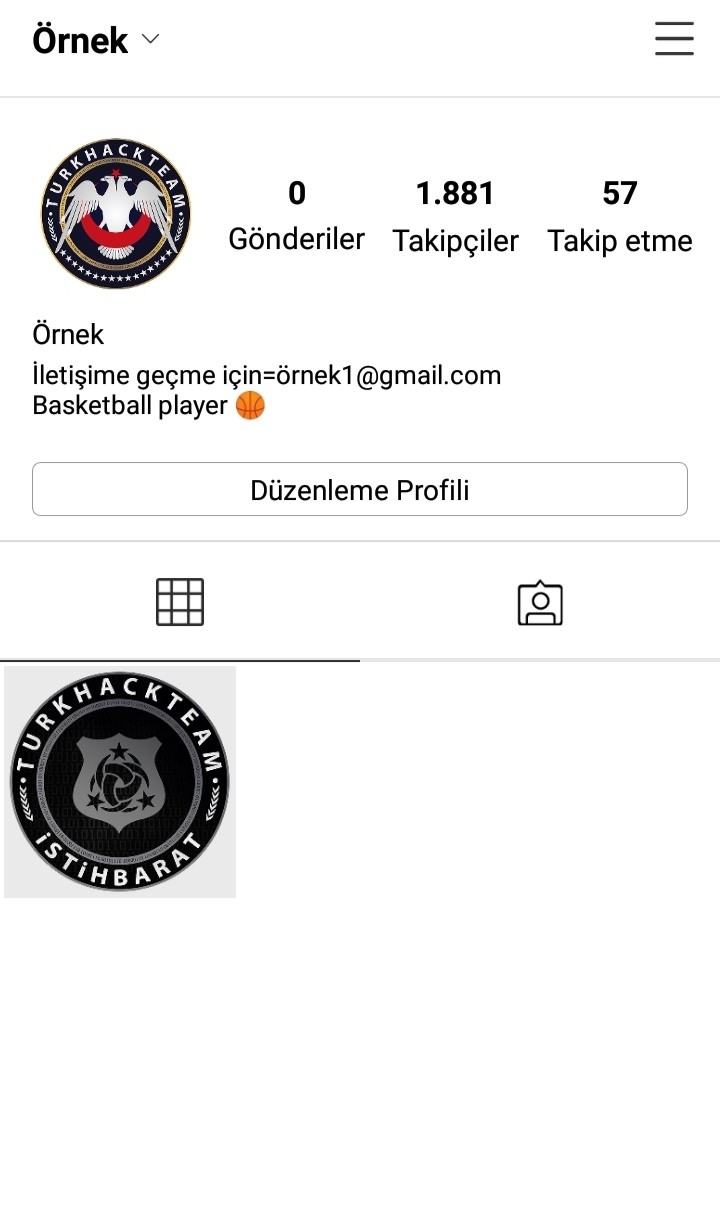
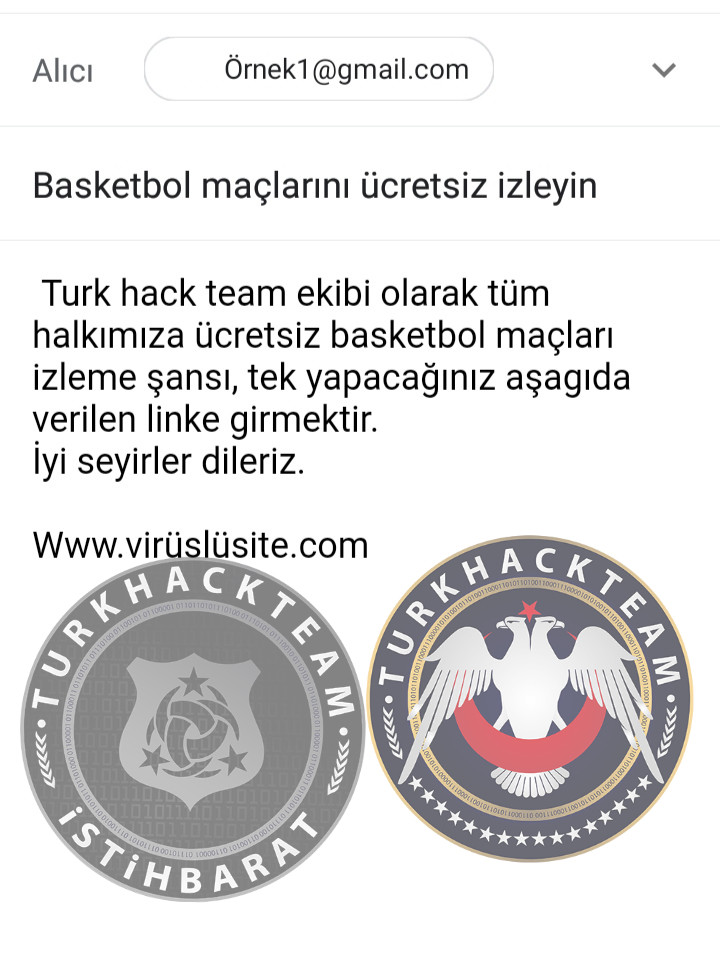
We see that the victim is interested in basketball. Our attack should be about basketball.
Arming
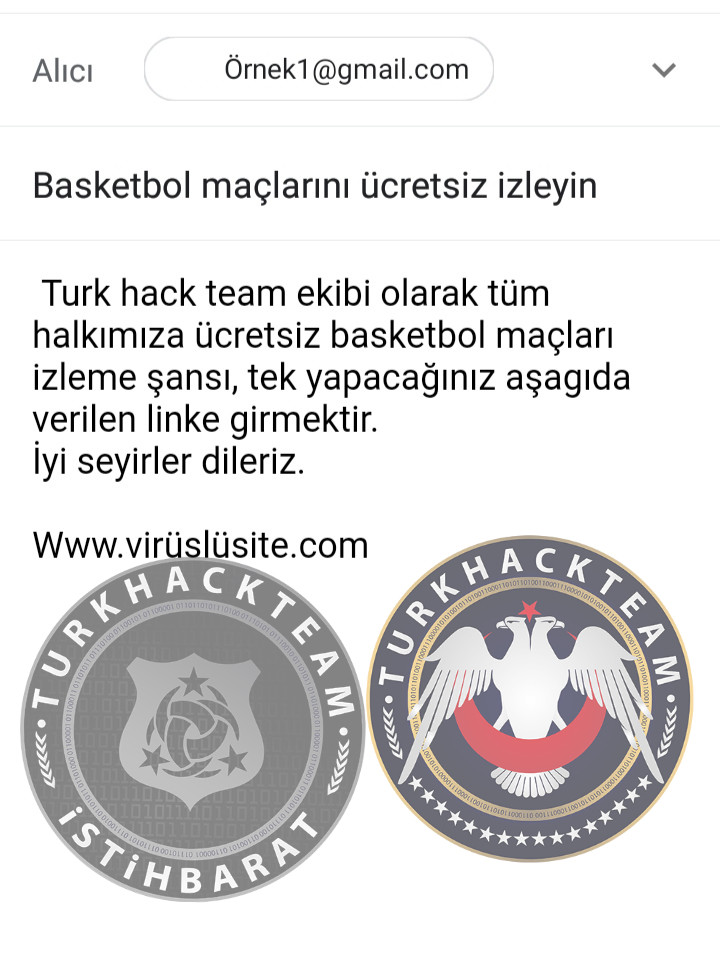
At this stage, tools are prepared. You discovered your victim's vulnerabilities. Let's say football attracts your victim's attention. You should write an article about football and put a link to this article. This is the second stage of the cyber kill chain.

Transmission
We created our virus and specified our victim's vulnerabilities. Now, we should send our virus to our victim via e-mail or social media platforms. This is the third stage of the cyber kill chain.
Exploitation
The victim clicked on the link. And our virus started to spread. This is the fourth stage of the cyber kill chain.

Setup
The virus completed the exploitation. It can hide and download files. Let me give you an example. I have been downloading 3 txt files called "crash_log1.txt" for 5 months on my device. I deleted it but it was keep coming. The virus was downloading these files to hide itself. Setup is the 5th stage of the cyber kill chain.

Command and Control
We completely take control of the victim's device. Now we can play with device settings, copying files, deleting files etc.

Targeted Action
We can crash the device or steal personal information if we want. This is the last stage of the cyber kill chain.
Note: These stages should be done regularly. If you make a mistake you are going to get in trouble for this.
Source: https://www.turkhackteam.org/sosyal-muhendislik/1904269-siber-olum-zinciri.html
Translator dRose98
Today I'm going to talk about Cyber Kill Chain. It is very important topic for you, if you want to become a hacker.

What is Cyber Kill Chain?
The cyber kill chain is a series of steps that trace stages of a cyberattack from the early reconnaissance stages to the exfiltration of data. The kill chain helps us to understand combat ransomware, security breaches, and advanced persistent attacks (APTs). The Cyber Kill Chain consist of 7 sections.

Cyber Kill Chain Stages
Discovery
Arming
Transmission
Exploitation
Setup
Command and Control
Targeted Action

Discovery
The attackers begin to investigate the victim's information. They start with searching the system and this is the first stage of the cyber kill chain.
We see that the victim is interested in basketball. Our attack should be about basketball.
Arming
At this stage, tools are prepared. You discovered your victim's vulnerabilities. Let's say football attracts your victim's attention. You should write an article about football and put a link to this article. This is the second stage of the cyber kill chain.

Transmission
We created our virus and specified our victim's vulnerabilities. Now, we should send our virus to our victim via e-mail or social media platforms. This is the third stage of the cyber kill chain.
Exploitation
The victim clicked on the link. And our virus started to spread. This is the fourth stage of the cyber kill chain.

Setup
The virus completed the exploitation. It can hide and download files. Let me give you an example. I have been downloading 3 txt files called "crash_log1.txt" for 5 months on my device. I deleted it but it was keep coming. The virus was downloading these files to hide itself. Setup is the 5th stage of the cyber kill chain.

Command and Control
We completely take control of the victim's device. Now we can play with device settings, copying files, deleting files etc.

Targeted Action
We can crash the device or steal personal information if we want. This is the last stage of the cyber kill chain.
Note: These stages should be done regularly. If you make a mistake you are going to get in trouble for this.
Source: https://www.turkhackteam.org/sosyal-muhendislik/1904269-siber-olum-zinciri.html
Translator dRose98
Moderatör tarafında düzenlendi: