- 7 Tem 2013
- 8,205
- 4
- 686

My purpose to show this post is to raise awareness of institutions and individuals, albeit a little. Its preventing serious damages in the cybersecurity area. Since its intended to be used for educational purposes, as you may harm third parties by using the information you have got, Turkhackteam does not accept any legal or criminal liability.

Now, some of our friends may call this method a historical artifact. Yeah, its very normal. Because it is a command-line utility included in Windows NT operating systems starting with Microsofts Windows 2000 operating system. It continues until today. It allows local or remote configuration of network devices like Modem Interface. Of course, it cant only provide the configuration but also view it. Here is a scenario: Lets say you have infiltrated the target system. So you can get the password of all profiles registered on the Wi-Fi network hardware of this target computer from the network structure. Thus, attacks can be organized against other people, or you can even forward people to specific target addresses accordingly. I found an article on a blog that caught my attention: Ill tell my teacher that Im going to fix his computer, but Ill find the schools internet password instead. Well, this is a good social engineering example.

Kod:
Kullanim: show profiles [[name=]] [interface=] [key=]
Parameters:
tags value
name - profile name.
interface - the interface on which it configures this profile
key - to display the key in plain text,
key=clear Set the value.
examples:
show profiles name=profil 1" interface="wireless network connection"
show profiles name="profil 2"
show profiles name="profil 3" key=clear
show profilesSECTION 1
Kod:
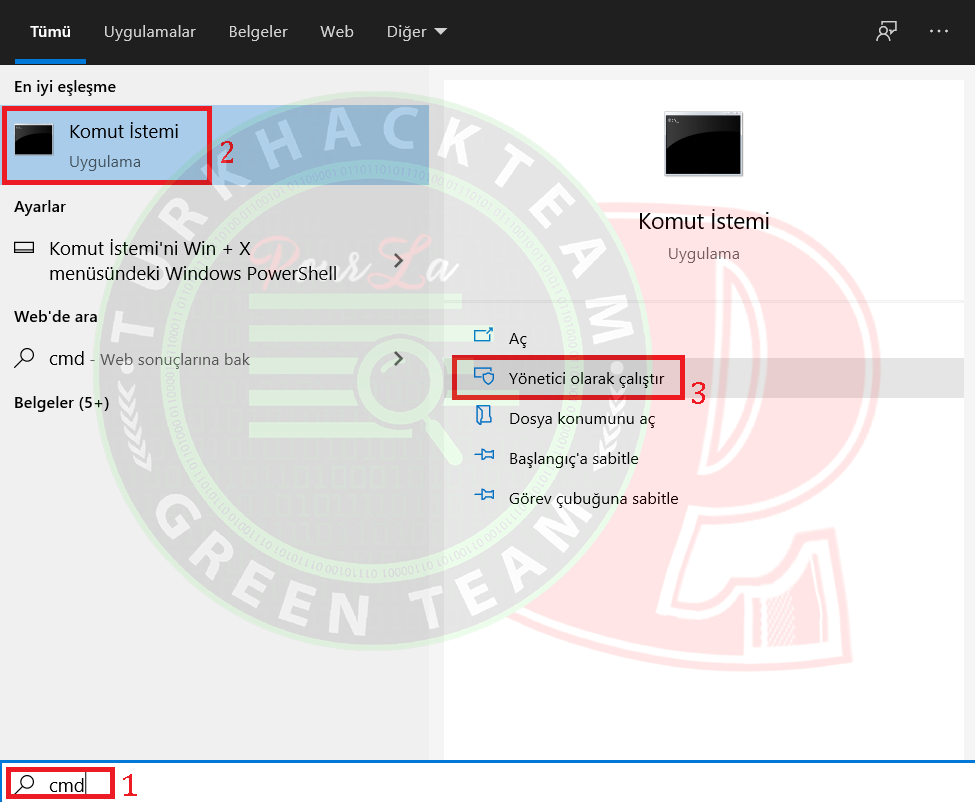
cmd>Command Prompt>Run as administrator.Its an MS-Dos-based coding console on Windows o.p devices.
SECTION 2
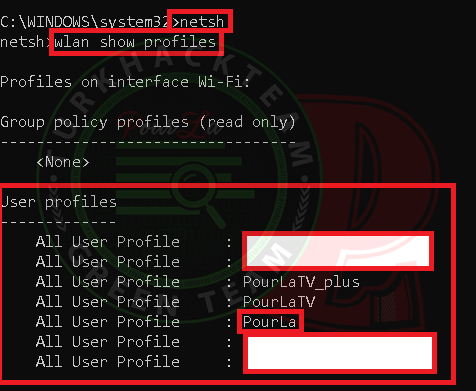
1) We run a tool by typing netsh #.
2) with WLAN show profiles #, we see all of the profiles in our network.
As you can see, all the profiles registered in our system came.
FINAL SECTION
Kod:
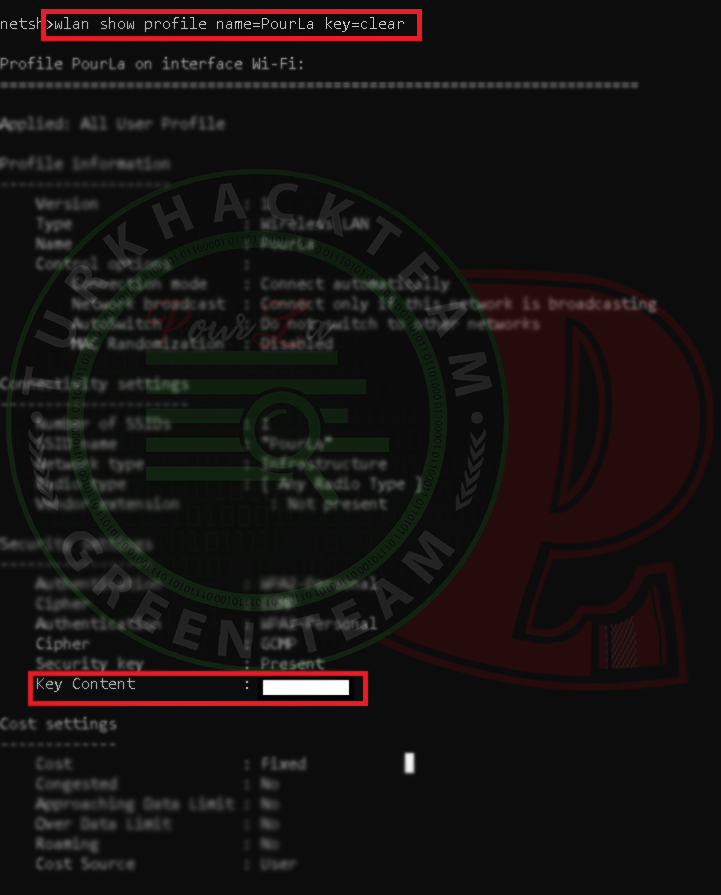
Wlan show profiles name=PourLa key=clearIn the key section, you can see the Wi-Fi password of the profile.
Knowing Reason &*Understanding the Cause
Kod:
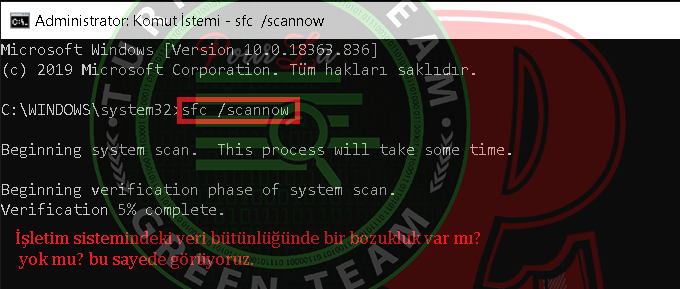
sfc /scannowIts a process we do to verify the data integrity of the operating system. When there is missing or corrupt data, we can see with this method. As you can see it couldnt find missing or corrupted data in my operating system. Of course, you can find it too manually and you can repair it.
(wlansvc) is not running Error
Kod:
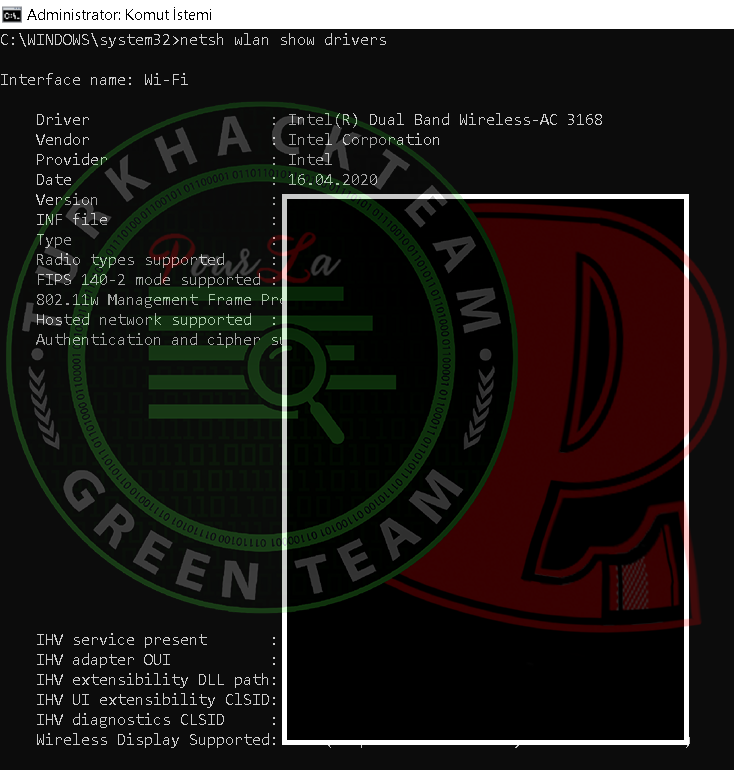
netsh WLAN show driversWe are questioning drivers. As you can see, it sees my card and I have no problem with it.
SOLUTION OF THE PROBLEM
Kod:
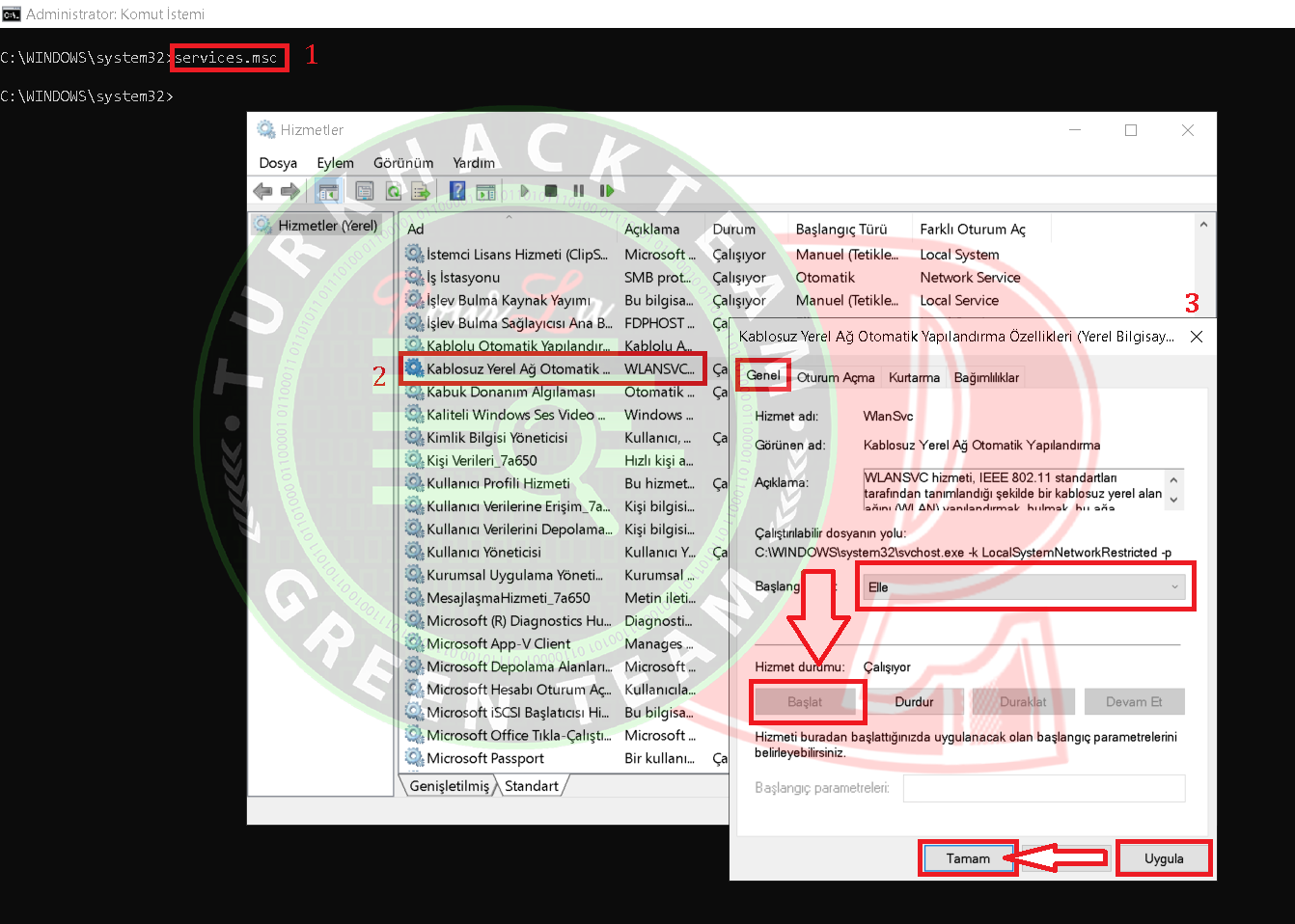
services.mscWith this command, we can make settings for Windows system service files. wlansvc is automatic. Were doing it manually. Its very simple: stop it, run it, apply the changes and thats it.

Source: https://www.turkhackteam.org/window...e-cokmek-windows-cmd-garip-bir-ag-yapisi.html
Çevirmen/Translator Gauloran
Son düzenleme: