- 21 Eki 2015
- 477
- 1
Protocols specify how the computer or server will contact to perform operations within itself.
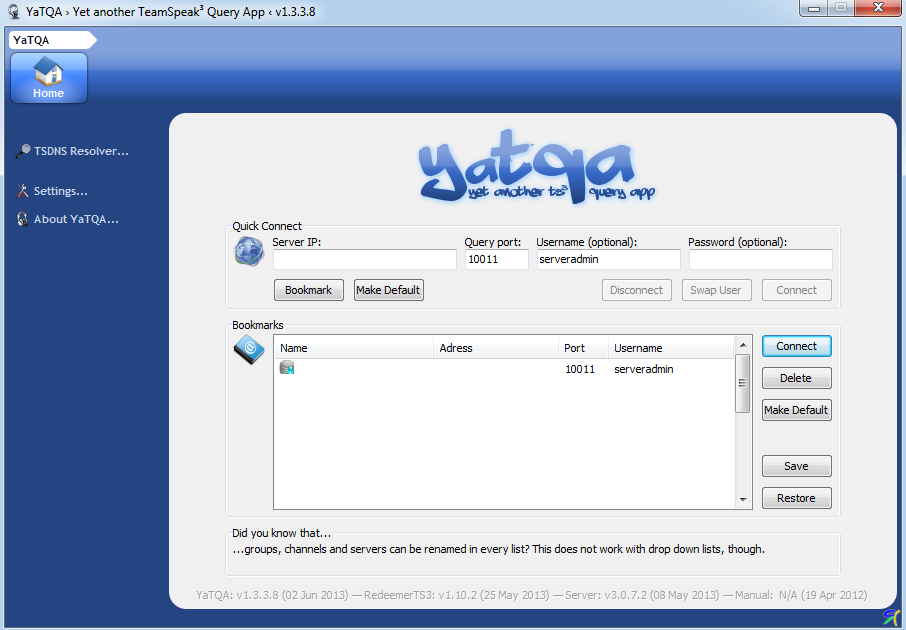
For example, let the 10011 port on our server be the tcp protocol. The 10011 port is known as the yatqa protocol.
When we open our application called YaTQa, it will call the 10011 protocol on its network and it will use it to perform the necessary operations within the server.
Protocols arent only used for software but also for hardware.
For example: We bought a new chip mouse. There is also a separate port that allows the management of this mouse on our computer. If that port is closed, the mouse will be disconnected if its l0cations remains the same.
Protocols act as a kind of wire to communicate in order to exchange data.
You need to write these codes to see the ports that are open our computer;
Use the following commands to see only the protocol of a specific port.
For example, let the 10011 port on our server be the tcp protocol. The 10011 port is known as the yatqa protocol.
When we open our application called YaTQa, it will call the 10011 protocol on its network and it will use it to perform the necessary operations within the server.
Protocols arent only used for software but also for hardware.
For example: We bought a new chip mouse. There is also a separate port that allows the management of this mouse on our computer. If that port is closed, the mouse will be disconnected if its l0cations remains the same.
Protocols act as a kind of wire to communicate in order to exchange data.
You need to write these codes to see the ports that are open our computer;
Kod:
netstatUse the following commands to see only the protocol of a specific port.
Kod:
netstat -aDisplays all connections and listening ports.
Kod:
netstat -bDisplays the executable file used when creating each connection or listening port. In some cases, known execution files contain more than one independent component and in these cases, the order of the components used to create connection or listening port is displayed. In this case, name of the executable file in [] at the bottom, the component it calls appears at the top and this format is continued until TCP/IP is reached. This option may take a lot of time to work and if your permissions are not sufficient, the operation fails.
Kod:
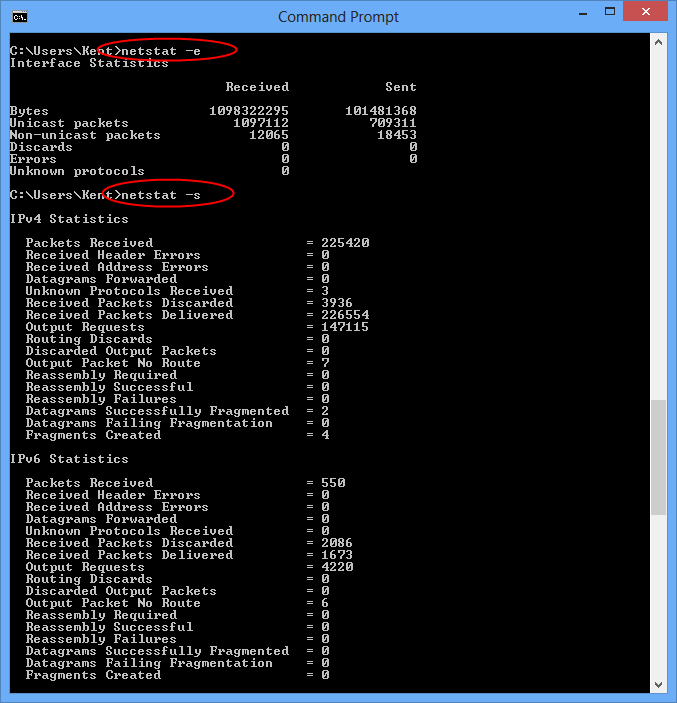
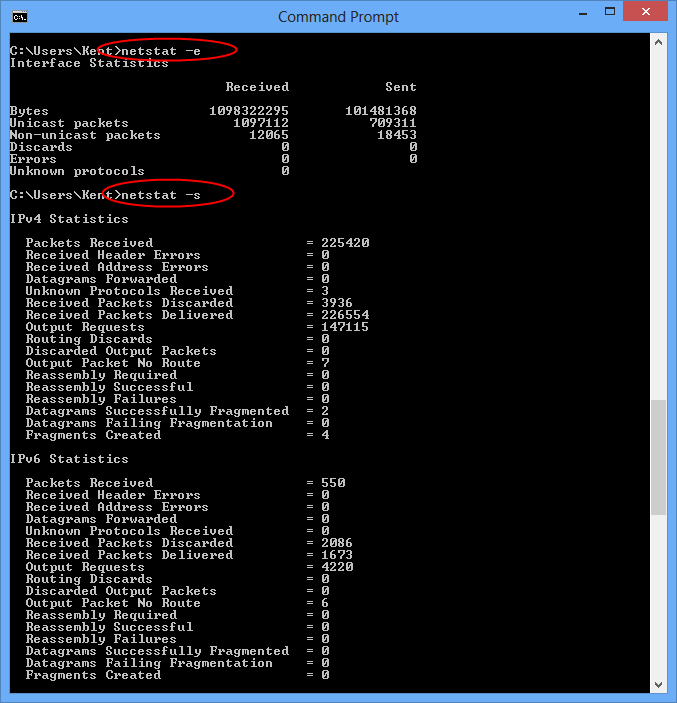
netstat -eDisplays Ethernet statistics. This can be combined with the -s option.
Kod:
netstat -fDisplays the fully qualified domain names <FQDN> for foreign addresses.
Kod:
netstat -nShows addresses and port numbers in number format.
Kod:
netstat -oDisplays the owner process ID associated with each connection.
Kod:
netstat -pIndicates the connections of the protocol specified in the Proto section. The Proto can be TCP, UDP, TCPv6 or UDPv6. When used with -s option to display statistics per protocol, the proto value can be IP, Ipv6, ICMP, ICMPv6, TCP, TCPv6, UDP and UDPv6.
Kod:
netstat -rDisplays the routing table.
Kod:
netstat -sDisplays individual statistics for each protocol. By default statistics for IP, Ipv6, ICMP, ICMPv6, TCP, TCPv6, UDP and UDPv6 are displayed; the -p option is used to specify a subset of the default field.
Kod:
netstat -tDisplays the current connection offload status.
Source: https://www.turkhackteam.org/window...kolleri-nedir-nasil-calisir-g4rib4n-reis.html
Translator: Provido
Translator: Provido
Moderatör tarafında düzenlendi:





