IP TRACER
It is a tool that provides us to have location information. This tool is really helpful for those who know how to use it. It provides us to do a great deal of screening for the location of the target in cyber intelligence. These issues are always connected to each other. When researching a person, it consist of an idea whether the information we found belongs to the target, so, it enables us to get closer to the target by making eliminations. Through this tool, we will be able to screen about the location of the target in pretty much. For example, let's assume we know the name and surname of the target and we have its IP, If we just search, we get a lot of different information from name and surname but In IP, by comparing with "state" we learned using it and the people in the results, we can make a big screen. So we reduced the situation from thousands to hundreds of people. If this situation is not enough, the first thing we need to do is to find the social media account belonging to the target, and we can provide the result with methods like photos of the current account, stories, relatives, photos of relatives. Well, how can we find the social media account? already the information we have only interconnected IP and name, we need to evaluate the accounts in the results related to "city" and "name" one by one. If you have extra information like "writing styles, thoughts, addresses, likes and dislikes", target you started the conversation and you can try to find the right account.
-Setup
& apt update
* Updates Packages.
& apt install git -y
* Installs the git package.
& git clone https://github.com/Rajkumrdusad/IP-Tracer.git
* Installs the Tool.
& cd IP-Tracer
* Enters inside the Folder.
& chmod +x install veya chmod 777 install
* Allows permissions to install.
& sh install veya ./install
* Runs the install.
& trace -m
* Shows our own IP.

& trace -t xxx.xxx.x.xxx (IP)
* Gives information about the target IP
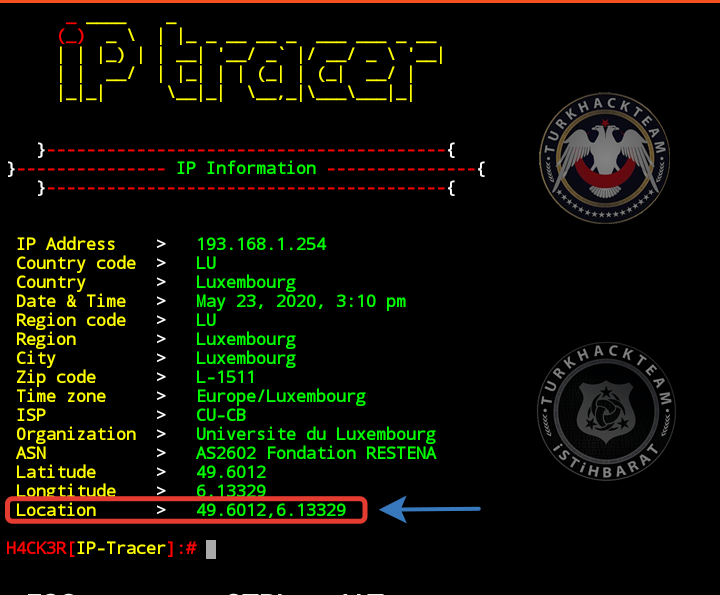
*We complete our process by reading the coordinates we found on the maps


-Other Parameters
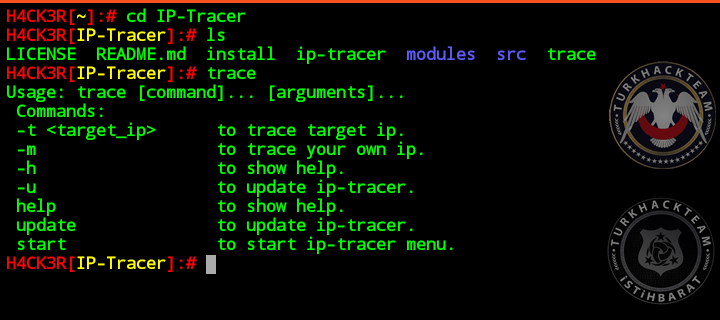
& trace
*We can see how we can update it and what we can do using the command.
*It gives information about the parameters that we can use.
*What we can do is limited by our imagination.
-You can get a lot of information that cannot be found on the internet. Toward with the information found, using social engineering at or near the target.
Source:İP-Tracer Kullanarak Yer Tespiti
Son düzenleme: