What is SUID / SGID Bit?
Let's assume we are an ordinary Linux user. So we are not root. If the changes that occur when we perform an operation as an ordinary user are also experienced in files that we can operate with root and only root authority, it is because SUID / SGID bits are actively working in that file directory. So these bits allow us to make changes to directories that we do not have permission to access. For this, I will give an example from passwd code in Linux. We can change our user password by using the passwd code. But we do this as an ordinary user without being root. However, if this password change is also happening in the / etc / shadow file that requires root authority, it is because the SUID bit in the / usr / bin / passwd binary file is enabled. SUID=Set User ID. SGID=Set Group ID. Let's look at these bits over Linux.
Is SUID / SGID Bit Active?
We are opening the Linux line of code.
Code:
ls -l /etc/passwd
We will look at the / etc / passwd file to see that bits work or don't work. This is normally a directory that we can only make changes with root authority.
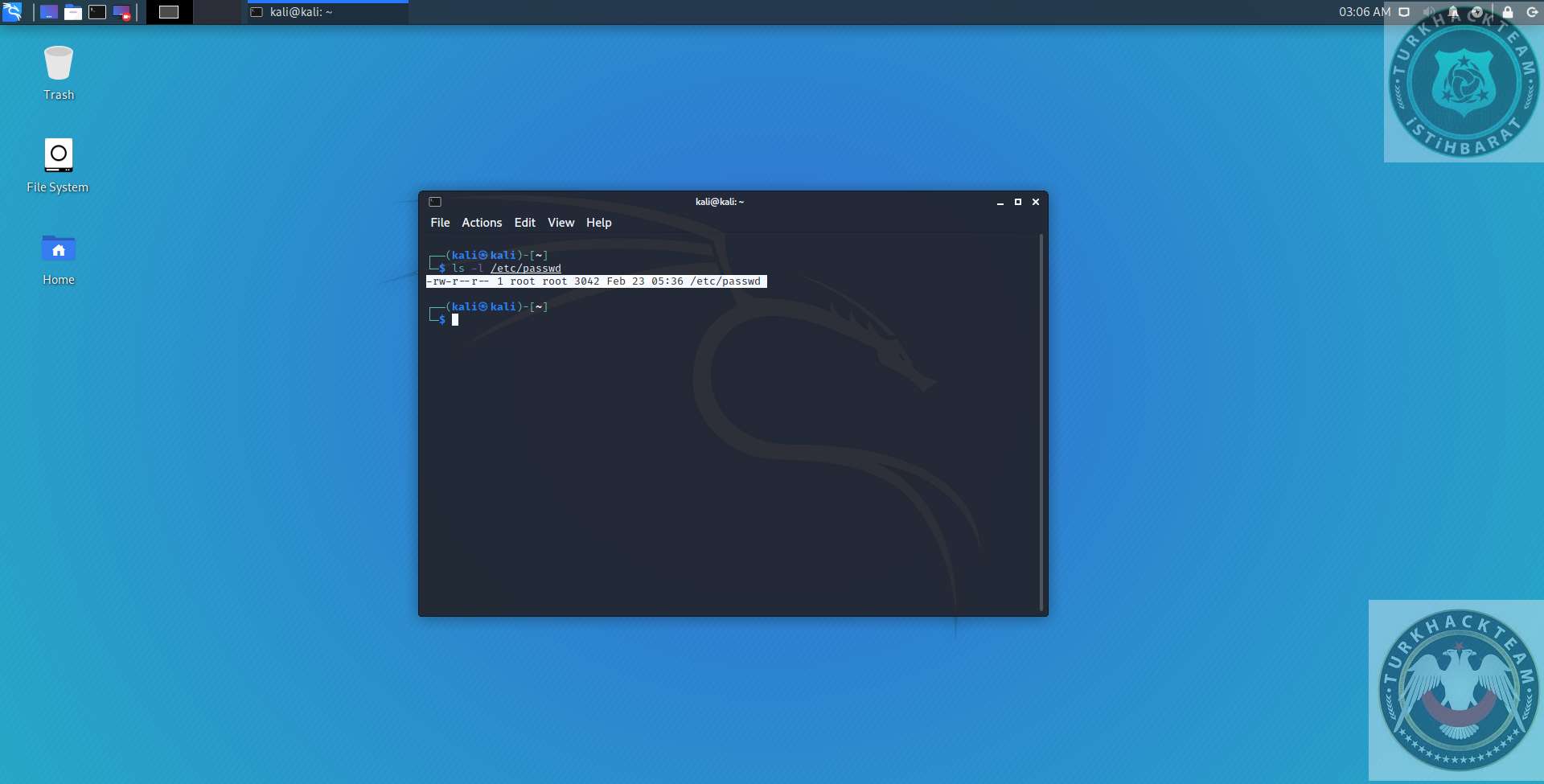
It will come output with this figure on the screen. When we look at this output, we are seeing that SUID SGID bits are not active in this directory. Where did we get that? If the SUID bit was active in this directory, our output would be like I will give in the manner.
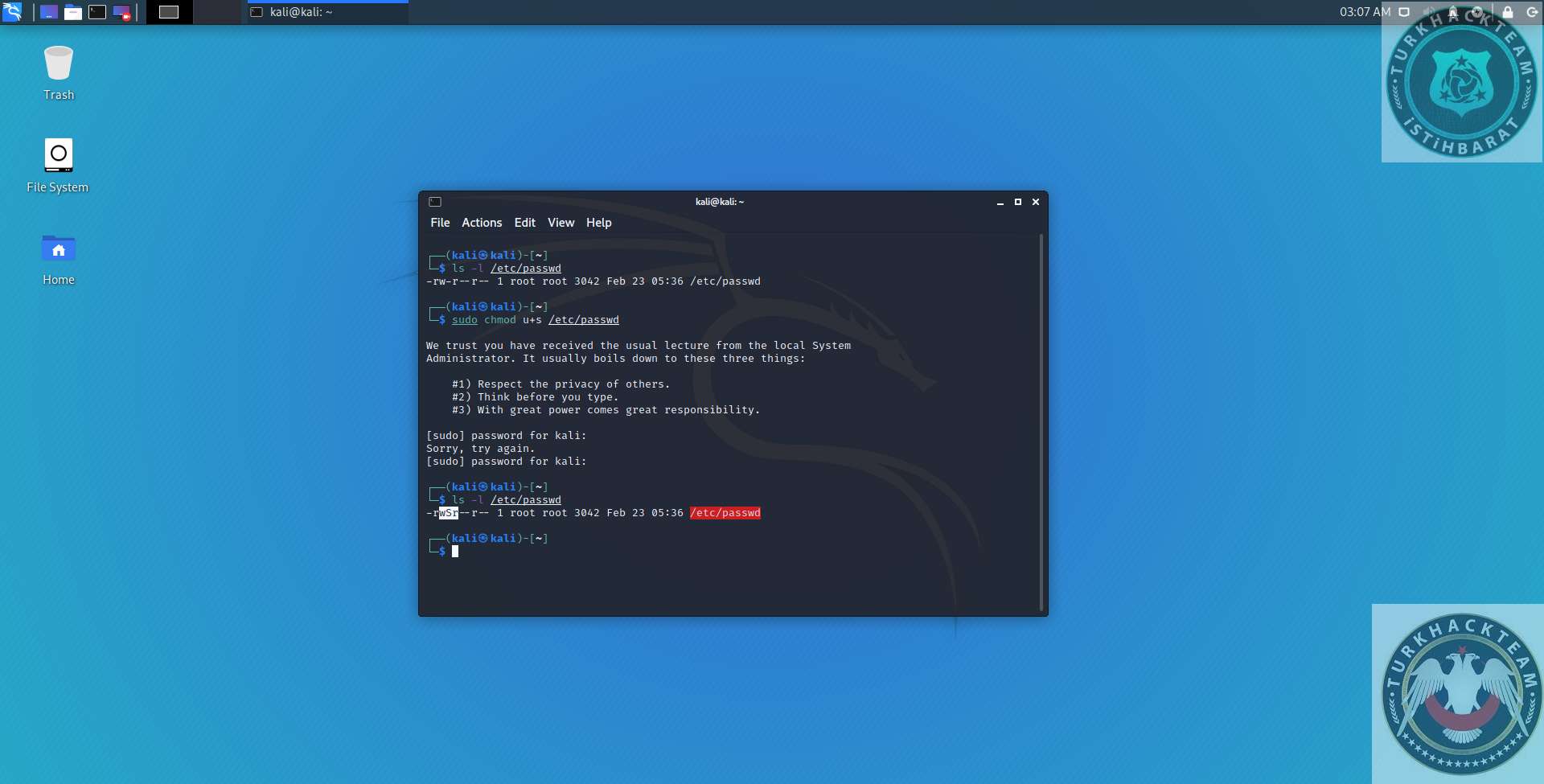
You do not look at the other codes you see in this output right now. I will explain them soon. If you pay attention to the place I chose with Mouse, there is an output called -rwSr. This tells us that SUID is active in this index and the action you will do will run here as root. In the just before printout, this (s) phrase did not exist. So I activated it and gave you this picture. If you look at the codes in the picture, you can see the (sudo chmod u + s / etc / passwd) code at the top. This code are benefiting us to enable the SUID bit in the directory we specified. u + s do this. The method in SGID is the same, and the g + s parameter is used in it. So the code we will use to enable;
Code:
sudo chmod u+s /etc/passwd
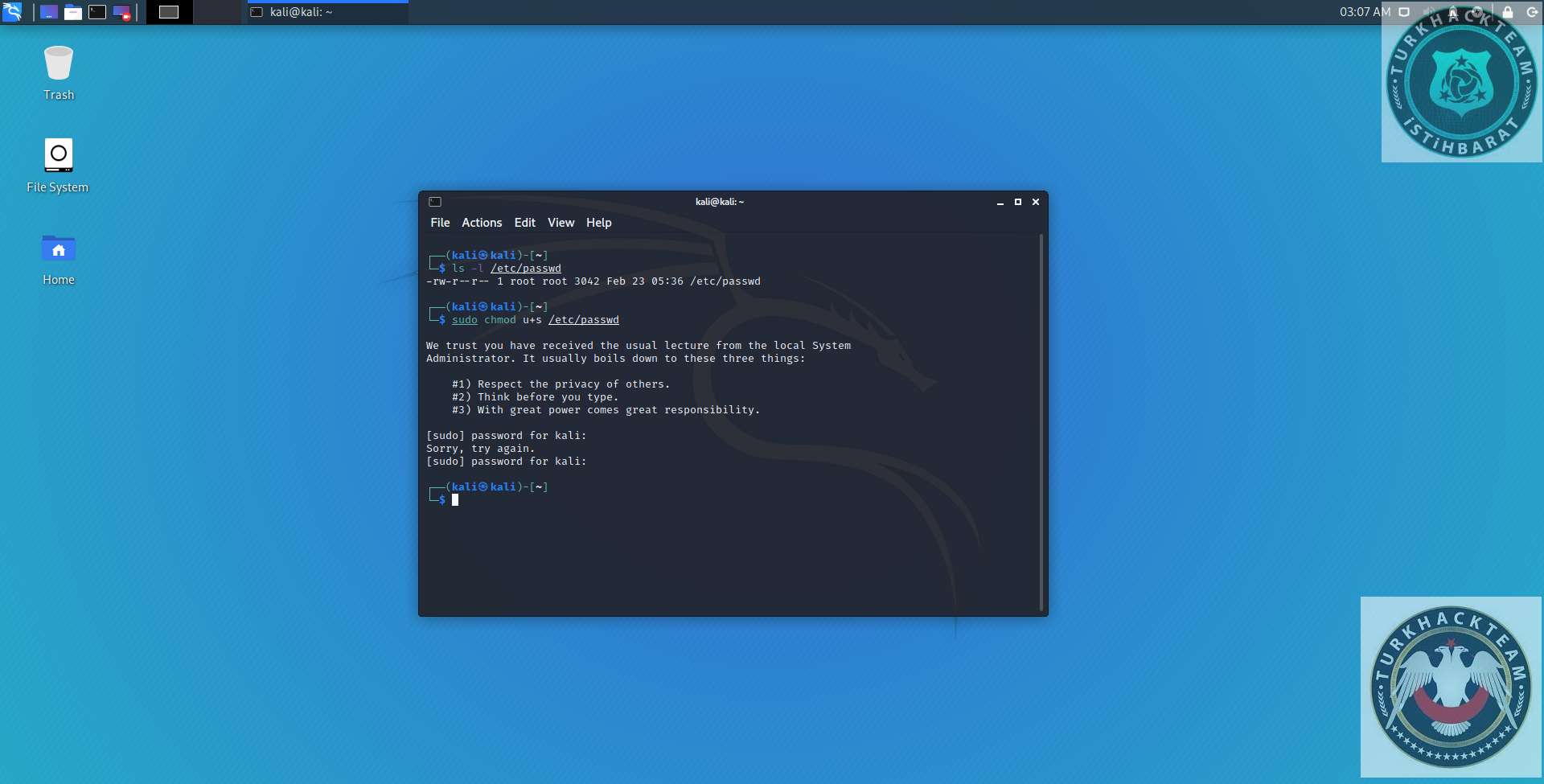
When you run this code it will give an output like this. When you enter it will ask you for your user password, the process will be completed. It said Sorry Try Again because I entered my password incorrectly. Let me point out that while typing the password, it seems to be not typed. When you run this code and run ls -l / etc / passwd again, you will see the (S) phrase I mentioned.
How is it in terms of security?
These bits may not be good for security. If a hacker who knows this is aware of these bits, the hacker can get root authority from the indexes where these bits are active in your Linux system and take over your system. As a precaution, it would be good to know the directories where these bits run regularly. The code we will use for this;
Code:
find / \( -perm -u+s -or -perm -g+s \) -type f -exec ls -l {} \;
This code will give us a very long output. But don't be confused, you will see in sub-section outputs the bits(-rwS etc.) and the indexes they work in. I did not want to give this printout for security reasons.
Source:https://www.turkhackteam.org/siber-guvenlik/1980688-suid-sgid-biti-neddir.html
Let's assume we are an ordinary Linux user. So we are not root. If the changes that occur when we perform an operation as an ordinary user are also experienced in files that we can operate with root and only root authority, it is because SUID / SGID bits are actively working in that file directory. So these bits allow us to make changes to directories that we do not have permission to access. For this, I will give an example from passwd code in Linux. We can change our user password by using the passwd code. But we do this as an ordinary user without being root. However, if this password change is also happening in the / etc / shadow file that requires root authority, it is because the SUID bit in the / usr / bin / passwd binary file is enabled. SUID=Set User ID. SGID=Set Group ID. Let's look at these bits over Linux.
Is SUID / SGID Bit Active?
We are opening the Linux line of code.
Code:
ls -l /etc/passwd
We will look at the / etc / passwd file to see that bits work or don't work. This is normally a directory that we can only make changes with root authority.
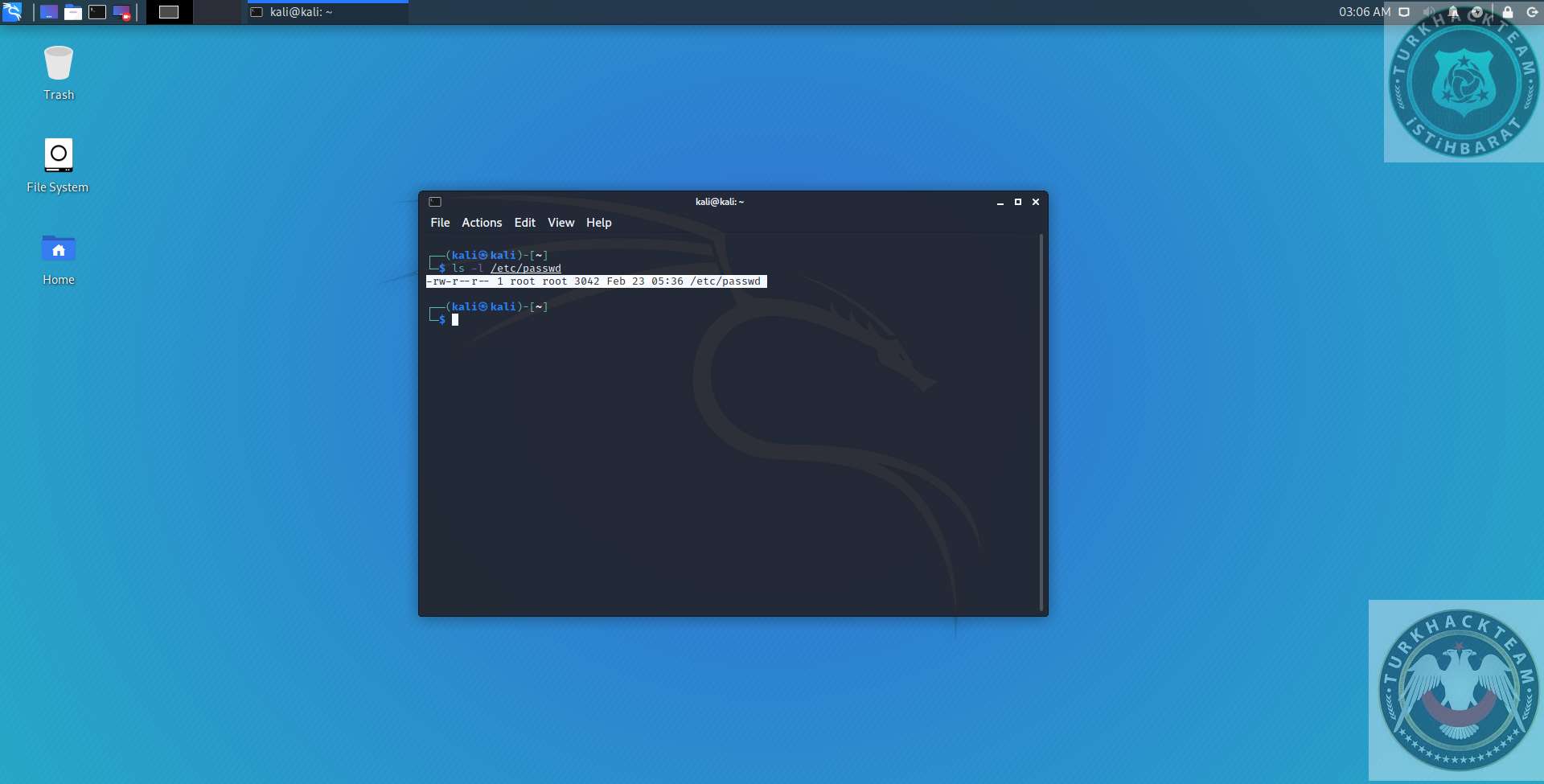
It will come output with this figure on the screen. When we look at this output, we are seeing that SUID SGID bits are not active in this directory. Where did we get that? If the SUID bit was active in this directory, our output would be like I will give in the manner.
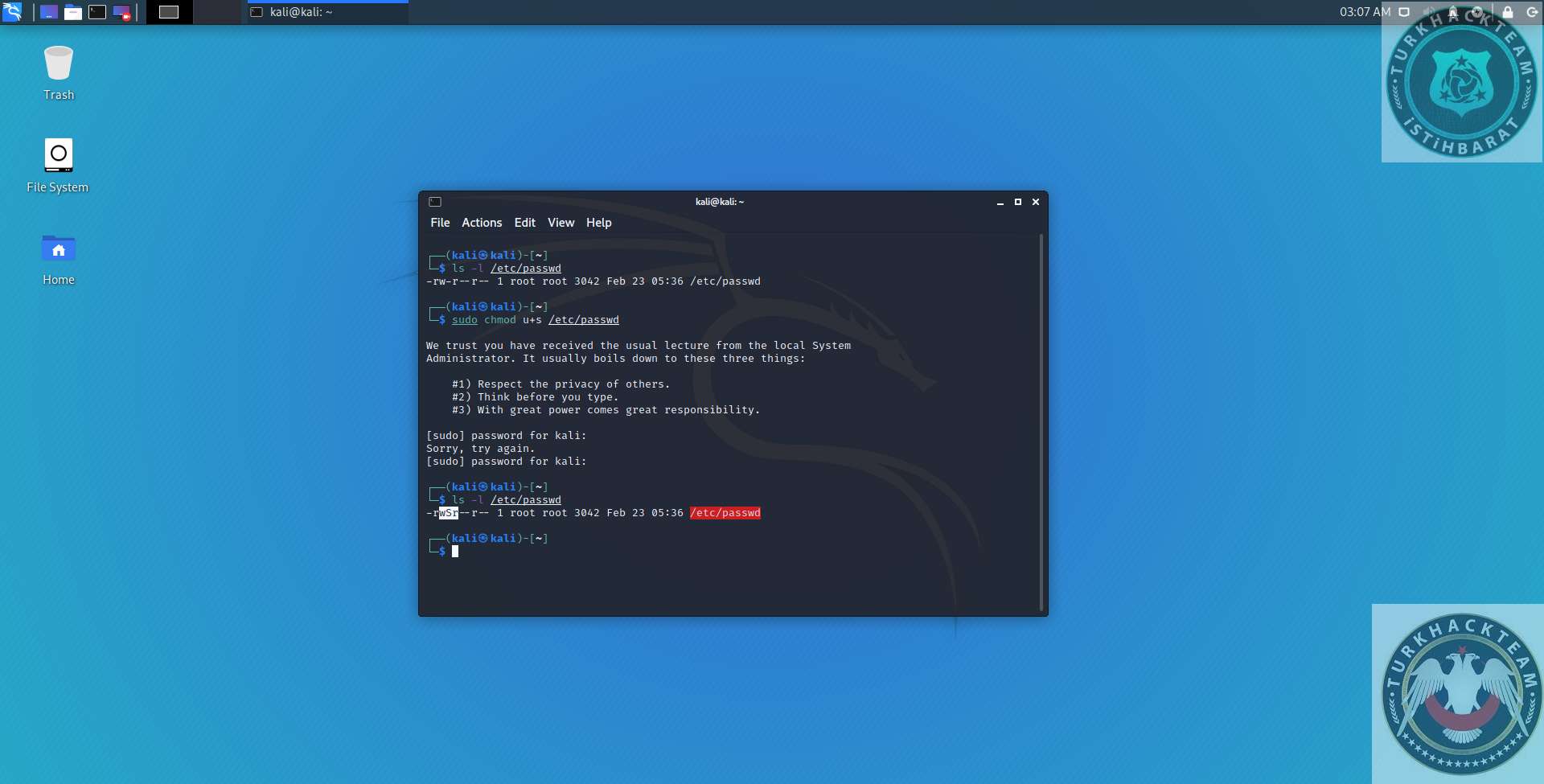
You do not look at the other codes you see in this output right now. I will explain them soon. If you pay attention to the place I chose with Mouse, there is an output called -rwSr. This tells us that SUID is active in this index and the action you will do will run here as root. In the just before printout, this (s) phrase did not exist. So I activated it and gave you this picture. If you look at the codes in the picture, you can see the (sudo chmod u + s / etc / passwd) code at the top. This code are benefiting us to enable the SUID bit in the directory we specified. u + s do this. The method in SGID is the same, and the g + s parameter is used in it. So the code we will use to enable;
Code:
sudo chmod u+s /etc/passwd
When you run this code it will give an output like this. When you enter it will ask you for your user password, the process will be completed. It said Sorry Try Again because I entered my password incorrectly. Let me point out that while typing the password, it seems to be not typed. When you run this code and run ls -l / etc / passwd again, you will see the (S) phrase I mentioned.
How is it in terms of security?
These bits may not be good for security. If a hacker who knows this is aware of these bits, the hacker can get root authority from the indexes where these bits are active in your Linux system and take over your system. As a precaution, it would be good to know the directories where these bits run regularly. The code we will use for this;
Code:
find / \( -perm -u+s -or -perm -g+s \) -type f -exec ls -l {} \;
This code will give us a very long output. But don't be confused, you will see in sub-section outputs the bits(-rwS etc.) and the indexes they work in. I did not want to give this printout for security reasons.
Source:https://www.turkhackteam.org/siber-guvenlik/1980688-suid-sgid-biti-neddir.html





